| | 1 | + | # Resources |
| | 2 | + | |
| | 3 | + | ## <mark style="color:green;">**Bug Bounty Resources & Disclosed Reports: A Valuable Collection of Insights 📝**</mark> |
| | 4 | + | |
| | 5 | + | * [Starting out](https://github.com/HolyBugx/HolyTips/tree/main/Resources#Starting-Out) |
| | 6 | + | * [Books](https://github.com/HolyBugx/HolyTips/tree/main/Resources#Books) |
| | 7 | + | * [Blogs](https://github.com/HolyBugx/HolyTips/tree/main/Resources#Blogs) |
| | 8 | + | * [Training Platforms](https://github.com/HolyBugx/HolyTips/tree/main/Resources#Training-Platforms) |
| | 9 | + | * [Web Security](https://github.com/HolyBugx/HolyTips/tree/main/Resources#Web-Security) |
| | 10 | + | * [Recon](https://github.com/HolyBugx/HolyTips/tree/main/Resources#Recon) |
| | 11 | + | * [XSS](https://github.com/HolyBugx/HolyTips/tree/main/Resources#XSS) |
| | 12 | + | * [CSRF](https://github.com/HolyBugx/HolyTips/tree/main/Resources#CSRF) |
| | 13 | + | * [IDOR](https://github.com/HolyBugx/HolyTips/tree/main/Resources#IDOR) |
| | 14 | + | * [Open Redirect](https://github.com/HolyBugx/HolyTips/tree/main/Resources#Open-Redirect) |
| | 15 | + | * [Race Condition](https://github.com/HolyBugx/HolyTips/tree/main/Resources#Race-Condition) |
| | 16 | + | * [Subdomain Takeover](https://github.com/HolyBugx/HolyTips/tree/main/Resources#Subdomain-Takeover) |
| | 17 | + | * [SSRF](https://github.com/HolyBugx/HolyTips/tree/main/Resources#SSRF) |
| | 18 | + | * [XXE](https://github.com/HolyBugx/HolyTips/tree/main/Resources#XXE) |
| | 19 | + | * [SQLi](https://github.com/HolyBugx/HolyTips/tree/main/Resources#SQLi) |
| | 20 | + | * [Misc](https://github.com/HolyBugx/HolyTips/tree/main/Resources#Misc) |
| | 21 | + | |
| | 22 | + | *** |
| | 23 | + | |
| | 24 | + | ### <mark style="color:green;">Starting-Out</mark> |
| | 25 | + | |
| | 26 | + | * [PortSwigger's Learning Path](https://portswigger.net/web-security/learning-path) |
| | 27 | + | * [Cobalt Vulnerability Wiki](https://cobalt.io/vulnerability-wiki/) |
| | 28 | + | * [OWASP Top 10 Web Training](https://application.security/free/owasp-top-10) |
| | 29 | + | * [OWASP Top 10 API Training](https://application.security/free/owasp-top-10-API) |
| | 30 | + | * [Web Security Course](https://web.stanford.edu/class/cs253/) |
| | 31 | + | |
| | 32 | + | *** |
| | 33 | + | |
| | 34 | + | ### <mark style="color:green;">Books</mark> |
| | 35 | + | |
| | 36 | + | * [The Web Application Hacker's Handbook, 2nd Edition](https://www.oreilly.com/library/view/the-web-application/9781118026472) |
| | 37 | + | * [Web Hacking 101](https://leanpub.com/web-hacking-101) |
| | 38 | + | * [Real-World Bug Hunting](https://www.amazon.com/gp/product/B072SQZ2LG) |
| | 39 | + | * [The Tangled Web](https://www.amazon.com/Tangled-Web-Securing-Modern-Applications/dp/1593273886) |
| | 40 | + | * [The Hacker Playbook 2](https://www.amazon.com/Hacker-Playbook-Practical-Penetration-Testing-ebook/dp/B01072WJZE) |
| | 41 | + | * [The Hacker Playbook 3](https://www.amazon.com/Hacker-Playbook-Practical-Penetration-Testing-ebook/dp/B07CSPFYZ2) |
| | 42 | + | |
| | 43 | + | *** |
| | 44 | + | |
| | 45 | + | ### <mark style="color:green;">Blogs</mark> |
| | 46 | + | |
| | 47 | + | * [Assetnote](https://blog.assetnote.io/) |
| | 48 | + | * [Secjuice](https://www.secjuice.com/) |
| | 49 | + | * [James Kettle](https://skeletonscribe.net/) |
| | 50 | + | * [Orange Tsai](https://blog.orange.tw/) |
| | 51 | + | * [Sam Curry](https://samcurry.net/blog/) |
| | 52 | + | * [Patrik Hudak](https://0xpatrik.com/) |
| | 53 | + | * [Honoki](https://honoki.net/) |
| | 54 | + | |
| | 55 | + | *** |
| | 56 | + | |
| | 57 | + | ### <mark style="color:green;">Training-Platforms</mark> |
| | 58 | + | |
| | 59 | + | * [BugBountyHunter.com](https://bugbountyhunter.com) |
| | 60 | + | * [PentesterLab](https://pentesterlab.com) |
| | 61 | + | * [HackTheBox](https://www.hackthebox.eu/home) |
| | 62 | + | * [TryHackMe](https://tryhackme.com) |
| | 63 | + | * [Rootme](https://www.root-me.org/?lang=en) |
| | 64 | + | * [PicoCTF](https://picoctf.org) |
| | 65 | + | * [GoogleCTF](https://capturetheflag.withgoogle.com) |
| | 66 | + | |
| | 67 | + | *** |
| | 68 | + | |
| | 69 | + | ### <mark style="color:green;">Web-Security</mark> |
| | 70 | + | |
| | 71 | + | * [Finding The Origin IP Behind CDNs](https://infosecwriteups.com/finding-the-origin-ip-behind-cdns-37cd18d5275) |
| | 72 | + | * [Accessing cross-site data using JSONP](https://www.sjoerdlangkemper.nl/2019/01/02/jsonp/) |
| | 73 | + | * [Hacking the SOP](https://medium.com/swlh/hacking-the-same-origin-policy-f9f49ad592fc) |
| | 74 | + | * [LocalStorage vs Cookie XSS](https://academind.com/tutorials/localstorage-vs-cookies-xss/) |
| | 75 | + | * [Cross-Site script inclusion](https://www.scip.ch/en/?labs.20160414) |
| | 76 | + | * [How to Hunt Bugs in SAML; a Methodology - Part I](https://epi052.gitlab.io/notes-to-self/blog/2019-03-07-how-to-test-saml-a-methodology/) |
| | 77 | + | * [How to Hunt Bugs in SAML; a Methodology - Part II](https://epi052.gitlab.io/notes-to-self/blog/2019-03-13-how-to-test-saml-a-methodology-part-two/) |
| | 78 | + | * [How to Hunt Bugs in SAML; a Methodology - Part III](https://epi052.gitlab.io/notes-to-self/blog/2019-03-16-how-to-test-saml-a-methodology-part-three/) |
| | 79 | + | * [SAML Attack Surface](https://github.com/kelbyludwig/saml-attack-surface) |
| | 80 | + | |
| | 81 | + | *** |
| | 82 | + | |
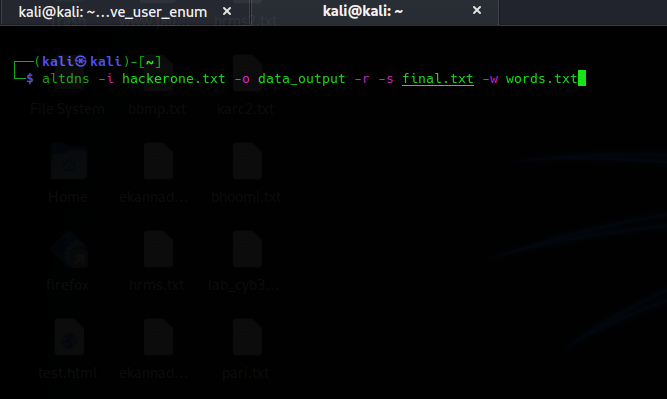
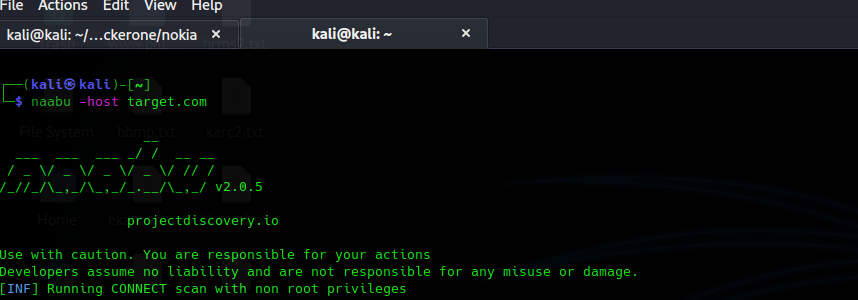
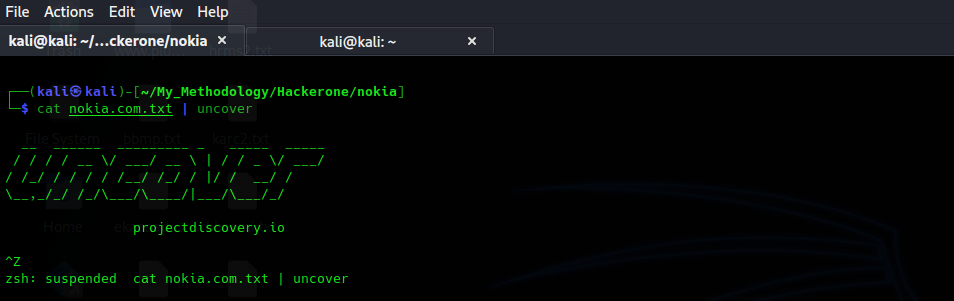
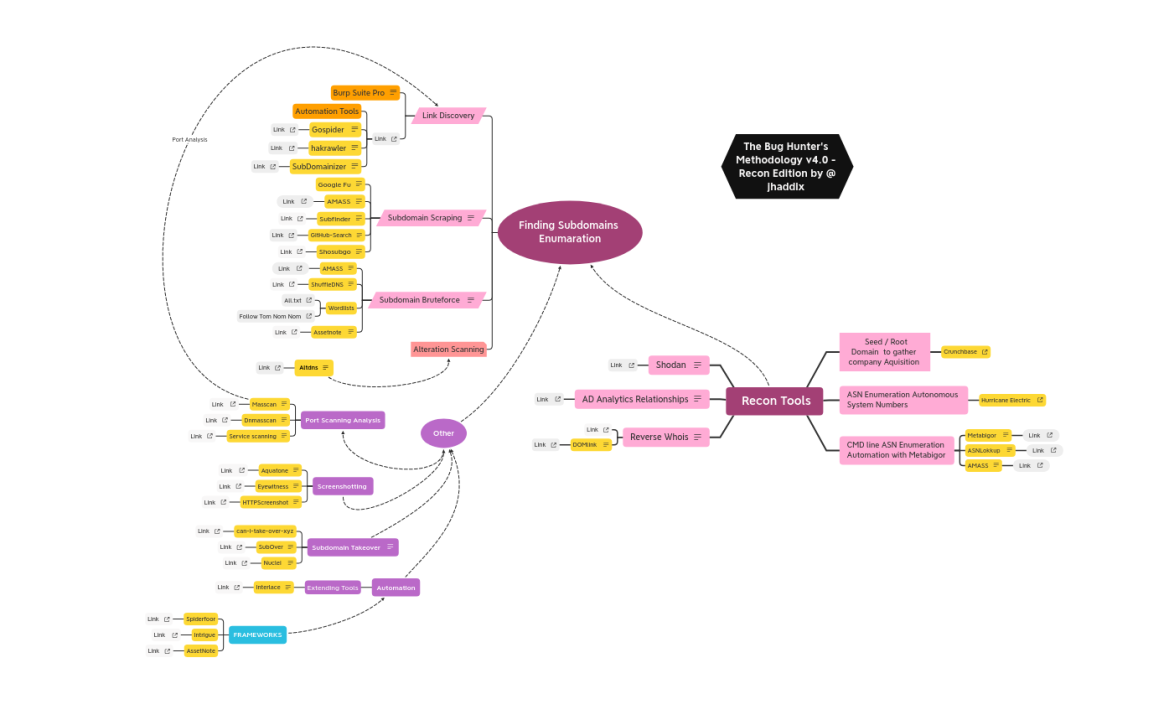
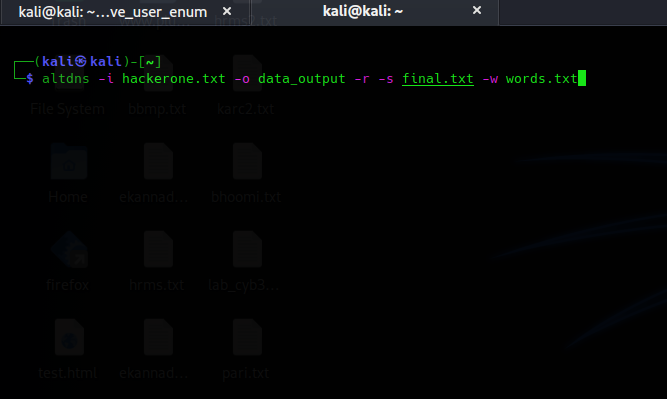
| | 83 | + | ### <mark style="color:green;">Recon</mark> |
| | 84 | + | |
| | 85 | + | * [The Bug Hunter's Methodology v4.0 - Recon Edition](https://youtu.be/p4JgIu1mceI) |
| | 86 | + | * [Fundamentals of Bug Bounty Recon](https://youtu.be/DABPWQ40yb0) |
| | 87 | + | * [How To Do Recon: Introduction to Recon](https://youtu.be/o8L2nweiF1s) |
| | 88 | + | * [Just another Recon Guide for Pentesters and Bug Bounty Hunters](https://www.offensity.com/de/blog/just-another-recon-guide-pentesters-and-bug-bounty-hunters/) |
| | 89 | + | * [The Best Bug Bounty Recon Methodology](https://securib.ee/beelog/the-best-bug-bounty-recon-methodology/) |
| | 90 | + | * [The Art of Subdomain Enumeration](https://appsecco.com/books/subdomain-enumeration/) |
| | 91 | + | |
| | 92 | + | *** |
| | 93 | + | |
| | 94 | + | ### <mark style="color:green;">XSS</mark> |
| | 95 | + | |
| | 96 | + | * [Instagram Reflected XSS](https://ysamm.com/?p=695) |
| | 97 | + | * [XSS in Facebook CDN](https://ysamm.com/?p=632) |
| | 98 | + | * [XSS on forums.oculusvr.com](https://ysamm.com/?p=525) |
| | 99 | + | * [Persistent DOM-based XSS in https://help.twitter.com via localStorage](https://hackerone.com/reports/297968) |
| | 100 | + | * [DOM XSS on app.starbucks.com via ReturnUrl](https://hackerone.com/reports/526265) |
| | 101 | + | * [XSS in steam react chat client](https://hackerone.com/reports/409850) |
| | 102 | + | * [XSS while logging using Google](https://hackerone.com/reports/691611) |
| | 103 | + | * [Stored XSS in RDoc wiki pages](https://hackerone.com/reports/662287) |
| | 104 | + | |
| | 105 | + | *** |
| | 106 | + | |
| | 107 | + | ### <mark style="color:green;">CSR</mark>F |
| | 108 | + | |
| | 109 | + | * [CSRF on connecting Paypal as Payment Provider](https://hackerone.com/reports/807924) |
| | 110 | + | * [CSRF on Periscope Web OAuth authorization endpoint](https://hackerone.com/reports/215381) |
| | 111 | + | * [CSRF combined with IDOR within Document Converter exposes files](https://hackerone.com/reports/398316) |
| | 112 | + | * [CSRF in all API endpoints when authenticated using HTTP Authentication](https://hackerone.com/reports/195156) |
| | 113 | + | * [The mass CSRFing of \*.google.com/\* products.](http://www.missoumsai.com/google-csrfs.html) |
| | 114 | + | * [Facebook CSRF bug which lead to Instagram Partial account takeover.](https://ysamm.com/?p=379) |
| | 115 | + | * [Media deletion CSRF vulnerability on Instagram](https://blog.darabi.me/2019/12/instagram-delete-media-csrf.html) |
| | 116 | + | * [Facebook CSRF protection bypass which leads to Account Takeover](https://ysamm.com/?p=185) |
| | 117 | + | |
| | 118 | + | *** |
| | 119 | + | |
| | 120 | + | ### <mark style="color:green;">IDOR</mark> |
| | 121 | + | |
| | 122 | + | * [IDOR bug to See hidden slowvote of any user even when you dont have access right](https://hackerone.com/reports/661978) |
| | 123 | + | * [IDOR allow access to payments data of any user](https://hackerone.com/reports/751577) |
| | 124 | + | * [IDOR Causing Deletion of any account](https://hackerone.com/reports/156537) |
| | 125 | + | * [IDOR allow to extract all registered email](https://hackerone.com/reports/302485) |
| | 126 | + | * [Another image removal vulnerability on Facebook](https://blog.darabi.me/2020/06/image-removal-vulnerability-on-facebook.html) |
| | 127 | + | * [Gsuite Hangouts Chat 5k IDOR](https://secreltyhiddenwriteups.blogspot.com/2018/07/gsuite-hangouts-chat-5k-idor.html) |
| | 128 | + | * [How I pwned a company using IDOR and Blind XSS](https://www.ansariosama.com/2017/11/how-i-pwned-company-using-idor-blind-xss.html) |
| | 129 | + | * [Disclose Private Dashboard Chart's name and data in Facebook Analytics](https://bugreader.com/jubabaghdad@disclose-private-dashboard-charts-name-and-data-in-facebook-analytics-184) |
| | 130 | + | |
| | 131 | + | *** |
| | 132 | + | |
| | 133 | + | ### <mark style="color:green;">Open-Redirect</mark> |
| | 134 | + | |
| | 135 | + | * [Open Redirects that matter](https://sites.google.com/site/bughunteruniversity/best-reports/openredirectsthatmatter) |
| | 136 | + | * [XSS and Open Redirect on MoPub Login](https://hackerone.com/reports/683298) |
| | 137 | + | * [XSS and Open Rredirect on supporthiring.shopify.com](https://hackerone.com/reports/158434) |
| | 138 | + | * [Open Redirect in secure.showmax.com](https://medium.com/@ahmadbrainworks/bug-bounty-how-i-earned-550-in-less-than-5-minutes-open-redirect-chained-with-rxss-8957979070e5) |
| | 139 | + | * [Open Redirect on streamlabs.com](https://hackerone.com/reports/978680) |
| | 140 | + | * [Open Redirect on "Language change"](https://hackerone.com/reports/52035) |
| | 141 | + | * [Open Redirect idp.fr.cloud.gov](https://hackerone.com/reports/387007) |
| | 142 | + | * [Airbnb chaining third party open redirect into SSRF via liveperson chat](https://buer.haus/2017/03/09/airbnb-chaining-third-party-open-redirect-into-server-side-request-forgery-ssrf-via-liveperson-chat/) |
| | 143 | + | * [Oauth authentication bypass on airbnb acquistion using wierd 1 char open redirect](https://xpoc.pro/oauth-authentication-bypass-on-airbnb-acquisition-using-weird-1-char-open-redirect/) |
| | 144 | + | |
| | 145 | + | *** |
| | 146 | + | |
| | 147 | + | ### <mark style="color:green;">Race-Condition</mark> |
| | 148 | + | |
| | 149 | + | * [Race Condition in performing retest allows duplicated payments](https://hackerone.com/reports/429026) |
| | 150 | + | * [Race Conditions in OAuth 2 API implementations](https://hackerone.com/reports/55140) |
| | 151 | + | * [Race Condition in Flash workers may cause an exploitable double free](https://hackerone.com/reports/37240) |
| | 152 | + | * [Exploiting a Race condition vulnerabililty](https://medium.com/@vincenz/exploiting-a-race-condition-vulnerability-3f2cb387a72) |
| | 153 | + | * [Race Condition leads to undeletable group member](https://hackerone.com/reports/604534) |
| | 154 | + | * [Race Condition on web](https://www.josipfranjkovic.com/blog/race-conditions-on-web) |
| | 155 | + | * [Race Condition in account survey](https://hackerone.com/reports/165570) |
| | 156 | + | * [Race Condition at create new Location](https://hackerone.com/reports/413759) |
| | 157 | + | |
| | 158 | + | *** |
| | 159 | + | |
| | 160 | + | ### <mark style="color:green;">Subdomain-Takeover</mark> |
| | 161 | + | |
| | 162 | + | * [Subdomain Takeover to Authentication bypass](https://hackerone.com/reports/335330) |
| | 163 | + | * [Subdomain Takeover on happymondays.starbucks.com due to non-used AWS S3 DNS record](https://hackerone.com/reports/186766) |
| | 164 | + | * [Subdomain Takeover on wfmnarptpc.starbucks.com](https://hackerone.com/reports/388622) |
| | 165 | + | * [Subdomain Takeover on svcgatewaydevus.starbucks.com and svcgatewayloadus.starbucks.com](https://hackerone.com/reports/383564) |
| | 166 | + | * [Subdomain Takeover: new level](https://medium.com/bugbountywriteup/subdomain-takeover-new-level-43f88b55e0b2) |
| | 167 | + | * [Subdomain Takeover on svcardproxydevus.starbucks.com](https://hackerone.com/reports/380158) |
| | 168 | + | * [Subdomain Takeover on blog.greenhouse.io pointing to Hubspot](https://hackerone.com/reports/38007) |
| | 169 | + | * [Subdomain Takeover on openapi.starbucks.com](https://hackerone.com/reports/241503) |
| | 170 | + | |
| | 171 | + | *** |
| | 172 | + | |
| | 173 | + | ### <mark style="color:green;">SSRF</mark> |
| | 174 | + | |
| | 175 | + | * [SSRF in Exchange leads to ROOT access in all instances](https://hackerone.com/reports/341876) |
| | 176 | + | * [SSRF using Javascript allows to exfill data from Google Metadata](https://hackerone.com/reports/530974) |
| | 177 | + | * [SSRF in Google cloud platform stackdriver](https://ngailong.wordpress.com/2019/12/19/google-vrp-ssrf-in-google-cloud-platform-stackdriver/) |
| | 178 | + | * [SSRF to ROOT Access](https://hackerone.com/reports/341876) |
| | 179 | + | * [SSRF reading local files from downnotifier server](https://www.openbugbounty.org/blog/leonmugen/ssrf-reading-local-files-from-downnotifier-server/) |
| | 180 | + | * [Facebook SSRF](https://medium.com/@amineaboud/10000-facebook-ssrf-bug-bounty-402bd21e58e5) |
| | 181 | + | * [31k$ SSRF in Google Cloud Monitoring led to metadata exposure](https://nechudav.blogspot.com/2020/11/31k-ssrf-in-google-cloud-monitoring.html) |
| | 182 | + | * [How I Chained 4 vulnerabilities on GitHub Enterprise, From SSRF Execution Chain to RCE!](http://blog.orange.tw/2017/07/how-i-chained-4-vulnerabilities-on.html) |
| | 183 | + | |
| | 184 | + | *** |
| | 185 | + | |
| | 186 | + | ### <mark style="color:green;">XXE</mark> |
| | 187 | + | |
| | 188 | + | * [XXE at ecjobs.starbucks.com.cn](https://hackerone.com/reports/500515) |
| | 189 | + | * [XXE on sms-be-vip.twitter.com in SXMP Processor](https://hackerone.com/reports/248668) |
| | 190 | + | * [XXE and SSRF on webmaster.mail.ru](https://hackerone.com/reports/12583) |
| | 191 | + | * [XXE in Site Audit function exposing file and directory contents](https://hackerone.com/reports/312543) |
| | 192 | + | * [Blind OOB XXE on ubermovement.com](https://hackerone.com/reports/154096) |
| | 193 | + | * [XXE over which leads to RCE](https://hackerone.com/reports/55431) |
| | 194 | + | * [LFI and SSRF via XXE in emblem editor](https://hackerone.com/reports/347139) |
| | 195 | + | * [Non-production Open Database In Combination With XXE Leads To SSRF](https://hackerone.com/reports/742808) |
| | 196 | + | |
| | 197 | + | *** |
| | 198 | + | |
| | 199 | + | ### <mark style="color:green;">SQLi</mark> |
| | 200 | + | |
| | 201 | + | * [Bypassing a crappy WAF to exploit a blind SQLI](https://robinverton.de/blog/2019/08/25/bug-bounty-bypassing-a-crappy-waf-to-exploit-a-blind-sql-injection/) |
| | 202 | + | * [Magix Bug Bounty: magix.com (RCE, SQLi) and xara.com (LFI, XSS)](https://www.rcesecurity.com/2014/04/magix-bug-bounty-magix-com-rce-sqli-and-xara-com-lfi-xss/) |
| | 203 | + | * [Tesla Motors blind SQLI](https://bitquark.co.uk/blog/2014/02/23/tesla\_motors\_blind\_sql\_injection) |
| | 204 | + | * [Blind SQL Injection on windows10.hi-tech.mail.ru](https://hackerone.com/reports/786044) |
| | 205 | + | * [Blind SQLi leading to RCE, from Unauthenticated access to a test API Webservice](https://hackerone.com/reports/592400) |
| | 206 | + | * [Step by Step Exploiting SQL Injection in Oculus](https://josipfranjkovic.blogspot.com/2014/09/step-by-step-exploiting-sql-injection.html) |
| | 207 | + | * [SQL Injection in lapsuudenturva](https://hackerone.com/reports/191146) |
| | 208 | + | * [SQL Injection Root Access tw.yahoo.com](https://buer.haus/2015/01/15/yahoo-root-access-sql-injection-tw-yahoo-com/) |
| | 209 | + | |

 Adwaith
committed
with
gitbook-bot
1 year ago
1 parent 95837b52
Adwaith
committed
with
gitbook-bot
1 year ago
1 parent 95837b52