| 1 | | - | # CVE-2023-25157 |
| 2 | | - | CVE-2023-25157 - GeoServer SQL Injection - PoC |
| | 1 | + | # CVE-2023-25157 - GeoServer SQL Injection - PoC |
| | 2 | + | |
| | 3 | + | - **CVE:** [CVE-2023-25157](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-25157) |
| | 4 | + | - **Date:** 06/06/2023 |
| | 5 | + | - **Vendor/Software:** [GeoServer](https://github.com/geoserver/geoserver) |
| | 6 | + | |
| | 7 | + | This script is a proof of concept for OGC Filter SQL Injection vulnerabilities in GeoServer, a popular open-source software server for sharing geospatial data. It sends requests to the target URL and exploits potential vulnerabilities by injecting malicious payloads into the `CQL_FILTER` parameter. |
| | 8 | + | |
| | 9 | + | ## Usage |
| | 10 | + | To use this script, provide the target URL as a command-line parameter. For example: |
| | 11 | + | ```console |
| | 12 | + | foo@bar:~$ python3 CVE-2023-25157.py <URL> |
| | 13 | + | ``` |
| | 14 | + | Replace `<URL>` with the actual URL of the target server. |
| | 15 | + | |
| | 16 | + | ## Google Dork |
| | 17 | + | ```inurl:"/geoserver/ows?service=wfs"``` |
| | 18 | + | |
| | 19 | + | 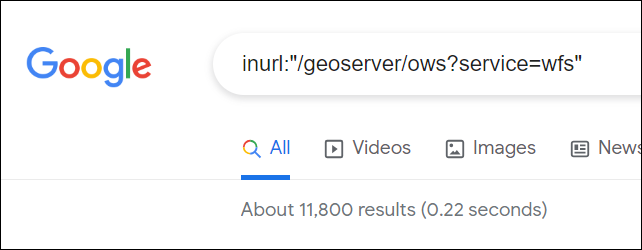 |
| | 20 | + | |
| | 21 | + | ## References |
| | 22 | + | 1. Security Advisory: [https://github.com/geoserver/geoserver/security/advisories/GHSA-7g5f-wrx8-5ccf](https://github.com/geoserver/geoserver/security/advisories/GHSA-7g5f-wrx8-5ccf) |
| | 23 | + | 2. Commit: [https://github.com/geoserver/geoserver/commit/145a8af798590288d270b240235e89c8f0b62e1d](https://github.com/geoserver/geoserver/commit/145a8af798590288d270b240235e89c8f0b62e1d) |
| | 24 | + | 3. Tweet: [https://twitter.com/parzel2/status/1665726454489915395](https://twitter.com/parzel2/status/1665726454489915395) |
| | 25 | + | |
| | 26 | + | **Script Author:** Bipin Jitiya ([@win3zz](https://twitter.com/win3zz)) |
| 3 | 27 | | |


 Bipin Jitiya
committed
with
GitHub
11 months ago
1 parent 234857e6
Bipin Jitiya
committed
with
GitHub
11 months ago
1 parent 234857e6